Note: This blog is now archived, and has been kept purely for historical and reference purposes. Updated blogs on this subject may appear on site in the future.
This blog is part of a series on Teams. For more articles, check back often
Written: 13/02/2022 | Updated: N/A
This series on Teams has been running for a while now – about two and half years. And during that time I’ve returned periodically to the subject of guests. Enabling/Disabling Guest Access in the TAC, purging from Azure AD, Self Service Removal, Sensitivity Labels, Entitlement Management. In the last few months I have covered Terms of Use, B2B Management Policy to block guest invitations and regulating guests with PIM and RBAC. But the perennial question – the elephant in the room as it were – has always been this “I have the tools now to control adding guests to my tenant but how can I – as an administrator – prevent my own users from joining other tenants as guests” How can I control that? Block that? Up until this point we would typically say one of two things. One – it’s the responsibility of the destination to control guest invitations even though typically we know from our own field experience that many orgs are always very active when it comes to guest management. Number two. It’s by design – and if we simply turn off Guest access lock stock then we shoot ourselves in the foot collaboratively. But reaching for that security and compliance hat as I have so often done of late, there is legitimate reasons that we may want to stop our own users being guests in other tenants. What if a competitor invites one of our users into their tenant to collaborate on something they aren’t supposed to? What is our users were spending most of their time as a guest in tenants that have nothing to do with our business? What if I as an admin want to limit certain users who are prone to accidental data leakage, or what if we just wanted to limit overall sprawl? So it should please administrators that we now have Cross Tenant Access Settings (CTAS) in preview which can do what we need. CTAS is defined as giving granular control over how external Azure AD organizations collaborate with you (inbound access) and how your users collaborate with external Azure AD organizations (outbound access). We’ll focus on outbound access in this one. To note right off the bat, this is designed to work with other Azure AD organizations – if for example you are working with other organisations who are non-AAD or have personal domains you’ll need to use Azure B2B Management. You’ll need Global Admin or Security Admin roles to configure – and AAD P1 licencing if you want to go granular with users or groups.
Let’s go.
This blog will cover
- Blocking outbound access to other Azure AD organisations for all applications for all users
- Blocking outbound access to other Azure AD organisations for all applications for some users
- Blocking outbound access to other Azure AD organisations for specific applications
- Blocking outbound access to specific Azure AD organisations
- Conclusion
Note this blog may have some abridged steps which will assume some experience with a Microsoft 365 environment and Azure AD
Prerequisites
- Global Administrator Role or Security Administrator Role (to configure)
- Azure AD P1 licences to configure for specific users and groups
- Microsoft 365 licence (With for example Teams) and a second tenant/lab for testing
BLOCKING OUTBOUND ACCESS TO OTHER AZURE AD ORGANISATIONS FOR ALL APPS FOR ALL USERS
Ok, before going granular we are going to do a simple broad sweeping block on the accessing of any Azure AD organisation outside of our own home tenant, for all users. The way this will be configured will essentially allow Guest Access Inbound and block all outbound. This is a good one to start with to explain the concept of defaults
1.) Login to https://login.microsoftonline.com

2.) From the waffle, or from the left app rail, select Admin
3.) In the Microsoft 365 admin centre, from the left navigation, select Show All and then Azure Active Directory
4.) From the left nav, select Azure Active Directory

5.) Select External Identities

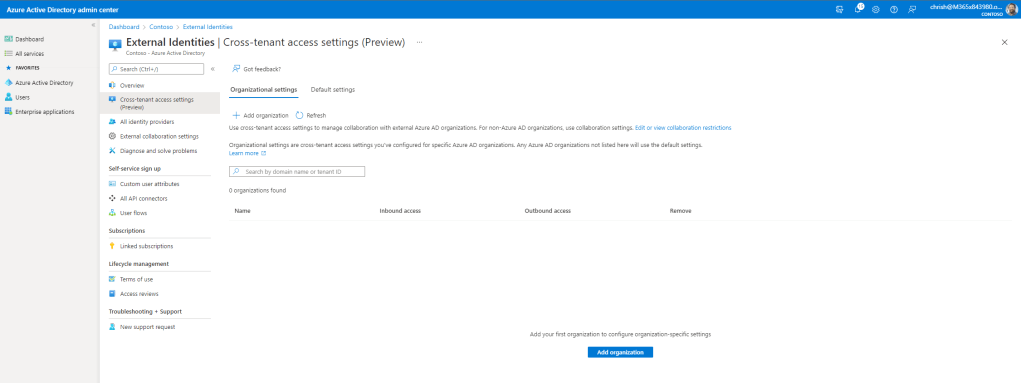
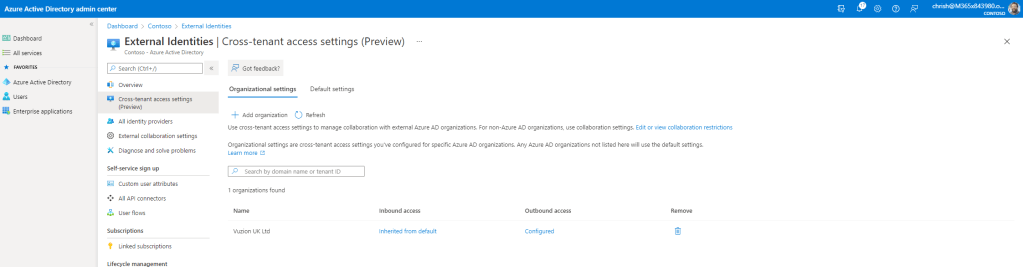
6.) Select Cross Tenant Access Settings (Preview)
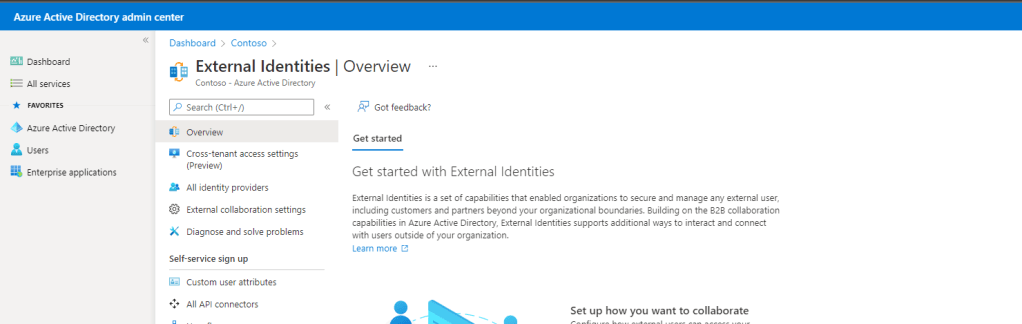
7.) At this point we see Organisational Settings and Default Settings. Organisational Settings are to set up Inbound and Outbound rules for specific organisations. In this example we want an all out block for all organisations for all users for outbound. To do this select Default Settings

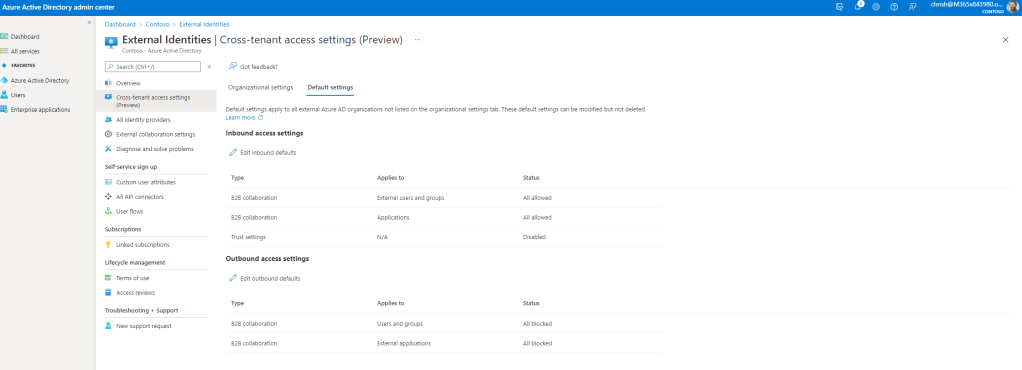
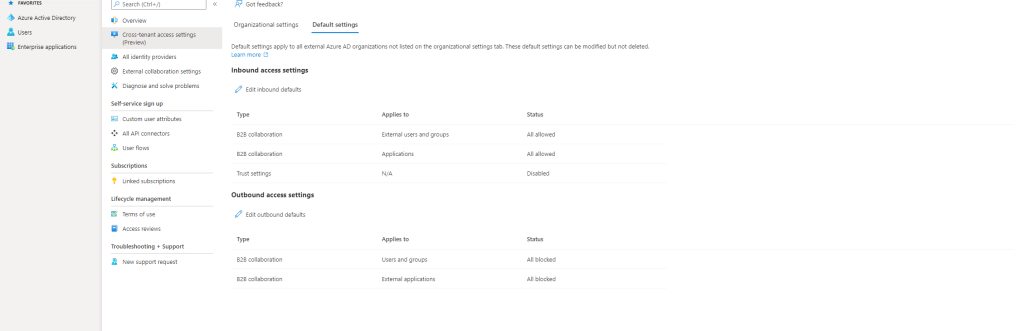
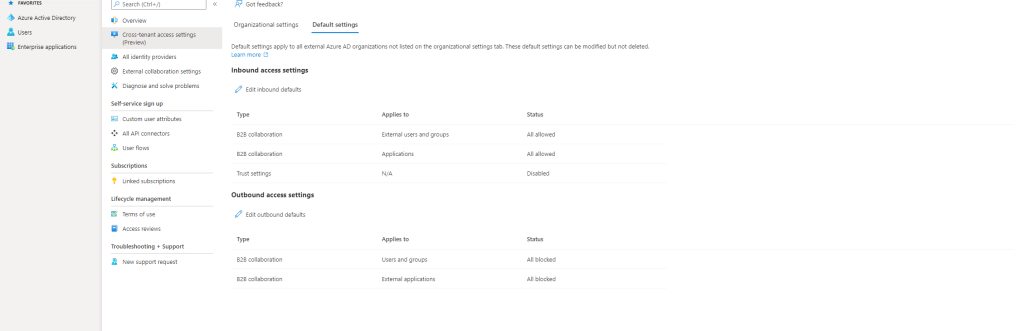
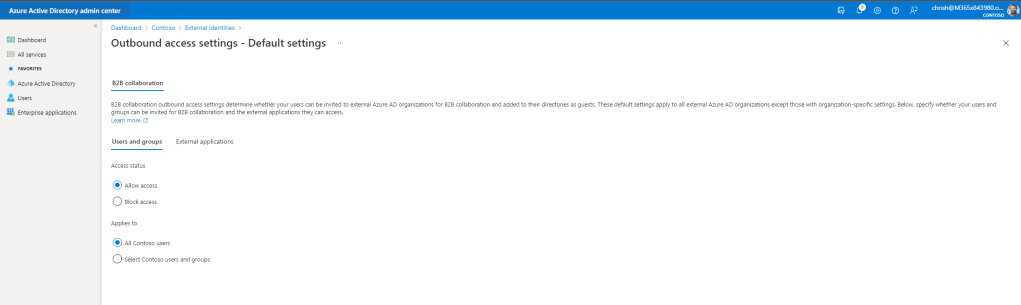
8.) As shown, Outbound Access is on by default. Select Edit Outbound Defaults
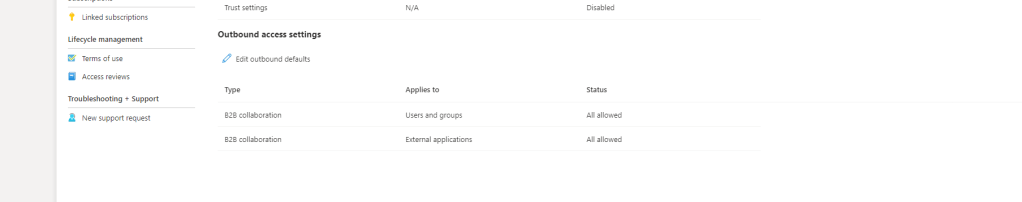
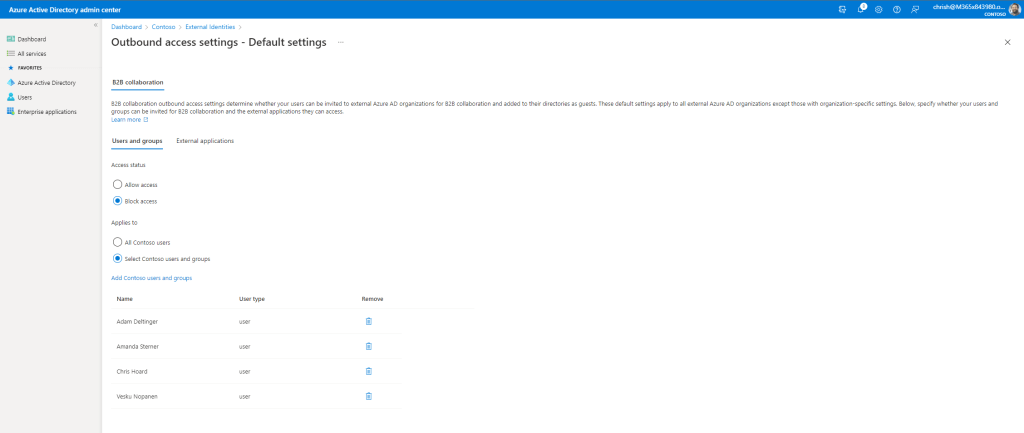
9.) Under Users and Groups then Access Status select Block Access
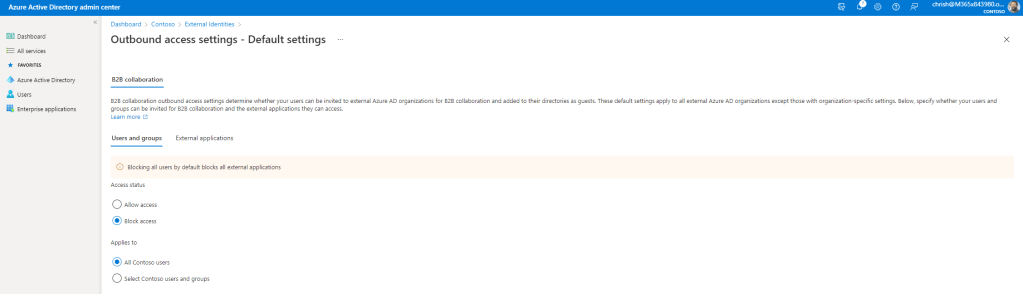
10.) Under External Applications then Access Status select Block Access and then Save
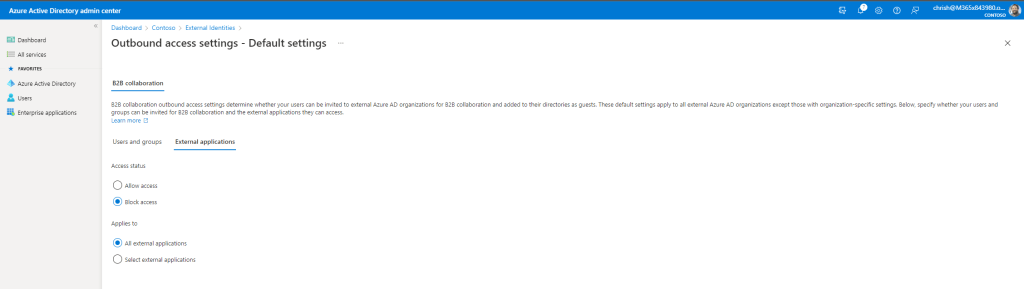
11.) Outbound Defaults for all users for all orgs are now changed to All Blocked
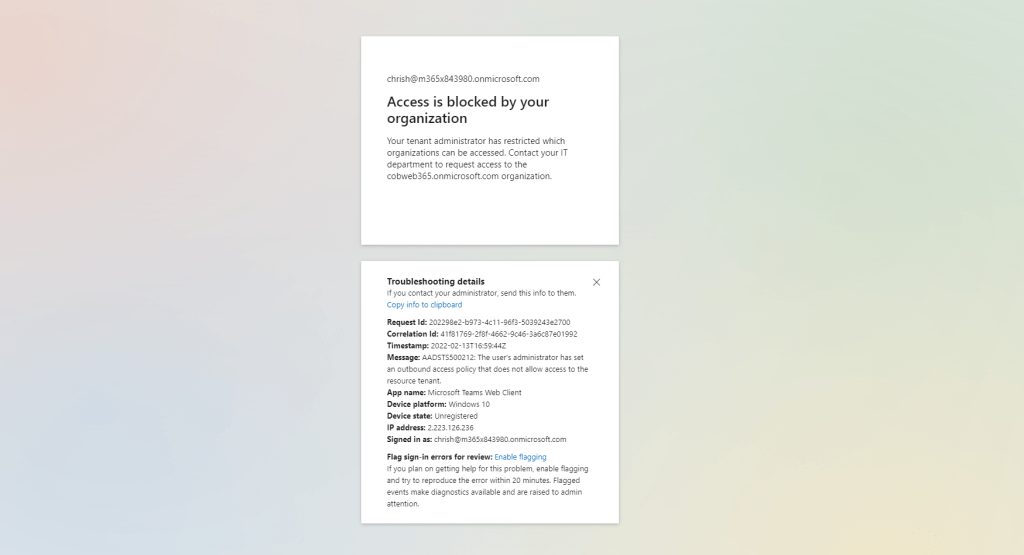
12.) So if someone outside my organisation invites a user to their tenant as a guest to collaborate in Teams my user will not be able to do so and they will receive a notification stating Access is blocked by your organisation as configured by me within CTAS in Azure AD

Our job here is done. Let’s look at a few more scenarios
BLOCKING OUTBOUND ACCESS TO OTHER AAD ORGANISATIONS FOR ALL APPS FOR SOME USERS
Ok, so we proved that we could essentially block all users to all apps with a broad brush amendment of the outbound defaults in CTAS. But it’s unlikely we’ll want to stop all users from accessing tenants outside of our own because some of our users will need to be guests and needed for things as projects or working with vendors, or co-authoring. However, some internal staff may not need to work in Teams within other tenants so why allow them to?
1.) Return to CTAS in Azure AD, select Default Settings

2.) Select Edit Outbound Defaults
3.) Under Users and Groups then Access Status select Block Access then under Applies To select [Organisation] Users or Groups to block and add your users and groups. Here shows 4 users in my org who I do not want to be guests in other organisations and have the ability to access their tenants
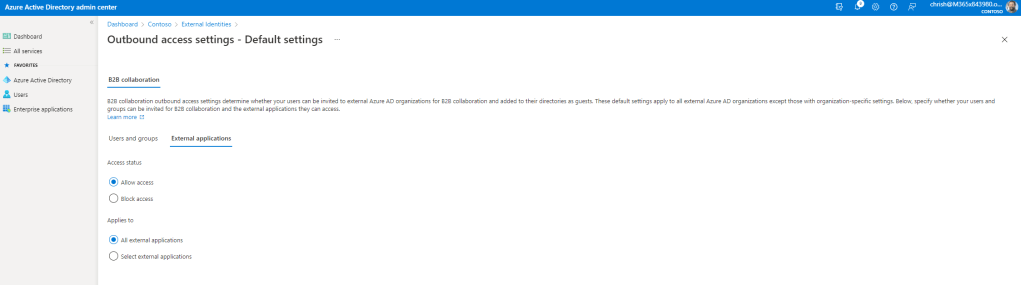
4.) Under External Applications select Allow Access and then Save
5.) The end result is this: the users who are blocked are blocked from accessing any external tenant so cannot be guests in any other organisation, whereas those who I do allow can access all applications in all other organisations, so they can be guests in apps such as Teams

BLOCKING OUTBOUND ACCESS TO OTHER AAD ORGANISATIONS FOR SPECIFIC APPLICATIONS
Ok, so we covered blocking all users to other AAD organisations, and we covered blocking some users. This will likely cover the most popular scenarios (at least in my experience). CTAS, as shown above, also allows us to block access to specific applications in other AAD environments. So imagine this, say I am ok with allowing my users access to SharePoint in other environments, but want to block access to Teams. How can I do that?
1.) Return to CTAS in Azure AD, select Default Settings

2.) Select Edit Outbound Defaults
3.) Under Users and Groups then Access Status select Allow All and under Applies To select All [Organisation] Users
4.) Under External Applications then Access Status select Allow Access. Under Applies To select Add Microsoft Application, search for and select applications, and leave out all the apps that you don’t want your users to access such as Teams. Select Save
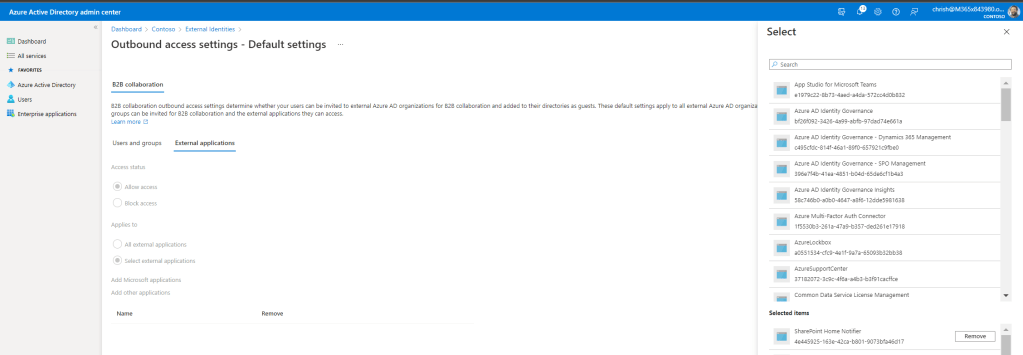

5.) Now that the default outbound access should be Some Allowed under External Applications
6.) If a user from my organisation tries to access an app not on the list, such as Teams, in another tenant where they have been invited as a guest, they will not be able to access it.
BLOCKING OUTBOUND ACCESS TO SPECIFIC AZURE AD ORGANISATIONS
We have looked at 3 scenarios so far: an all out block outbound for all users for all apps, an outbound block on some users, and a block on users to access specific apps in other organisations tenants. The last scenario is blocking outbound for specific organisations. The first three scenarios modified the defaults in CTAS to achieve it: but amending the defaults means the settings apply to all other organisations. What if we just want to stop users being guests or accessing specific tenants, such as competitors? We can do this with CTAS too.
1.) Under Default Settings we set everything back to Allowed. This means all our users can access all other tenants, and be guests in all other organisations, like when Teams was first deployed

2.) Select Organisational Settings then Add Organisation
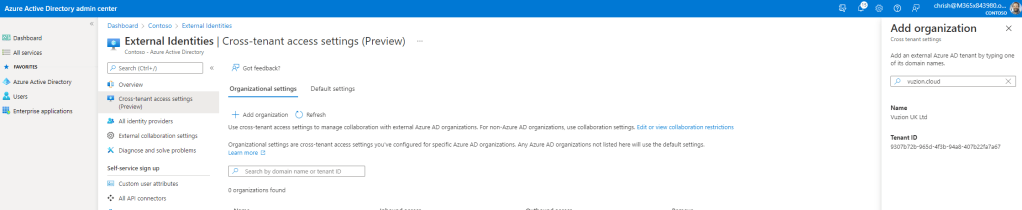
3.) Search for and add the Organisations Domain. Azure AD will identify the other organisations tenant – then select Add
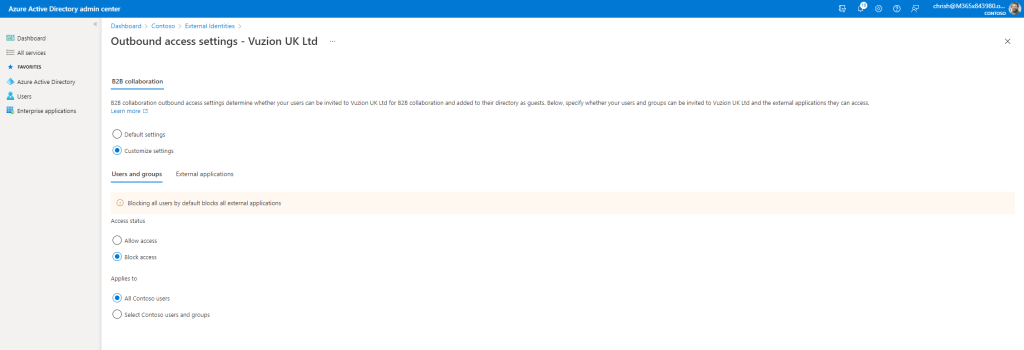
4.) By default Azure AD will use the defaults. Under Outbound Access select the hyperlinked Inherited from Default
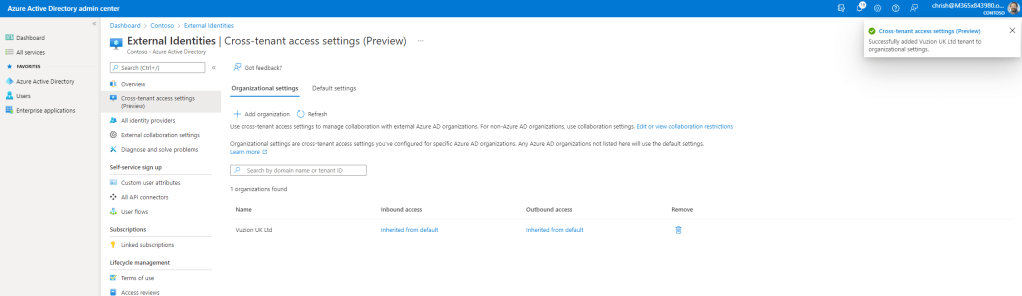
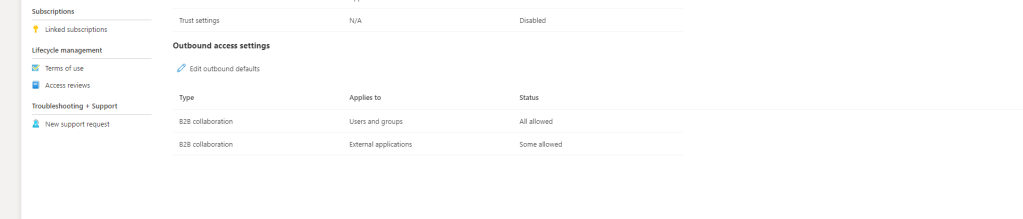
5.) Select Customise Settings and then configure users and groups and external applications as in the steps above when configuring the defaults. Here, for example, I have added an all out block on all users and all apps trying to access this specific organisation. Once done select Save
6.) Outbound access is configured for this specific organisation. Whereas none of my users will be able to access this specific organisation, they will be able to access all others if that is permitted by the defaults

CONCLUSION
A strong add by Microsoft. It’s a functionality which has been asked for a long time, and which can be used alongside Azure B2B Management in External Identities. It gives administrators more control. It allows organisations to be more compliant where they are required to be so via regulation. It does not have to mean completely all out blocking your users accessing external tenants or being guests in other organisations: it can be granulated by users and groups, or by applications, or apply to specific organisations who pose a threat or risk such as competitors. Overall, I feel it fills in a big gap. It’s sure to go down well with many in the Microsoft Tech Community. In the next few weeks, we’ll turn our attention to Inbound and comparison with Azure B2B Management where they would be used together


One thought on “[Archived] Teams Real Simple with Pictures: You want to block your own users being guests in other tenants? Well, now, you can with Cross Tenant Access Settings”
Comments are closed.