Note: This blog is now archived, and has been kept purely for historical and reference purposes. Updated blogs on this subject may appear on site in the future.
Written: 15/05/2022 | Updated: N/A
Its Sunday night. 9pm. I am teaching Microsoft 365 Fundamentals the next few days. I am speaking at Build the week after. So you know the score. Yes – that’s right it’s Jack Bauer time all over again. And so this week I’m gonna change tack (yet again) and return to talking about Azure AD: this time about authenticator notifications and lighting up two preview functionalities. The first is Number Matching which requires users to enter the number displayed on the sign-in screen, and Additional Context which adds the app the user is signing into as well as their IP location. Why are these important? Well, imagine a user who simply – without thought – approves an authenticator request when it pops up on their device. What if that approval isn’t actually legit at all. What if it’s a malicious actor who has phished the users credentials and knows that if they periodically enter the username and password, that there is a high probability the user will approve the request. By default authenticator doesn’t ask you to take any further actions apart from approval or denial nor does it make you second guess that. It doesn’t give you any information to say what app is being accessed or where they are signing in from. If I put my security hat on that’s problematic especially when accessing apps such as Teams which could contain a lot of sensitive information. So two nice adds to the authentication experience. They make the user more mindful and this should – in theory at least – harden the security posture.
Let’s go.
This blog will cover
- Enabling Number Matching and Additional Context in Azure AD
- Accessing Teams after configuring Azure AD
Prerequisites
- Global Admin permissions (To configure Azure AD) or a lesser privileged role such as Authentication Policy Administrator
- Teams Licence (Within Microsoft 365 Licence) for testing
To note, this blog will assume that the user involved is enabled for Multifactor Authentication, Microsoft Authenticator has been enabled in Azure AD and that a user has installed the Authenticator app via the Apple store and enrolled
ENABLING NUMBER MATCHING AND ADDITIONAL CONTEXT IN AZURE AD
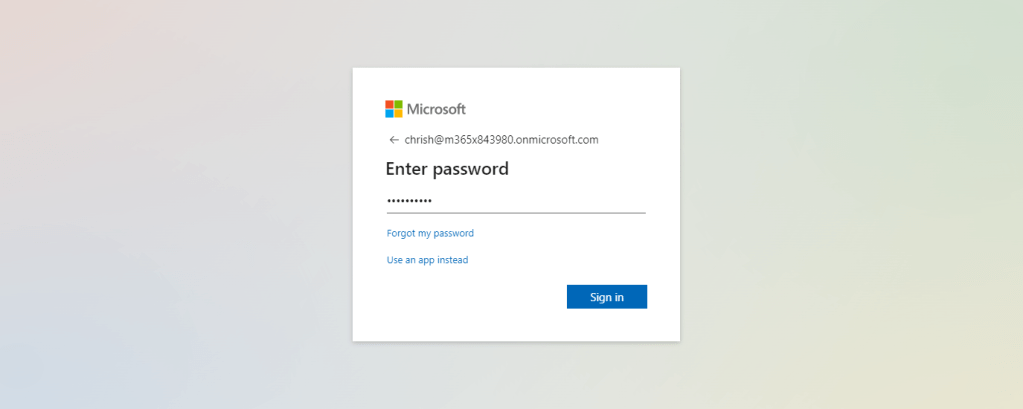
1.) Login with administrator credentials to https://login.microsoftonline.com
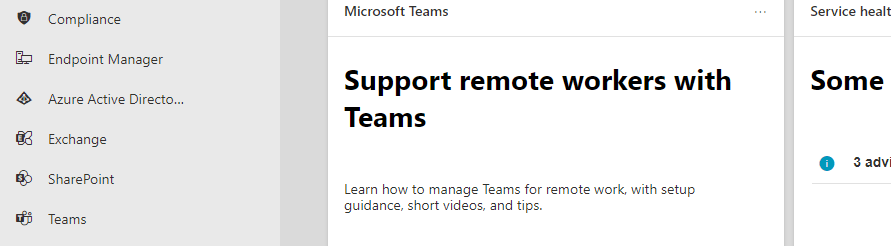
2.) From the left app rail, or via the waffle (top left) select Admin
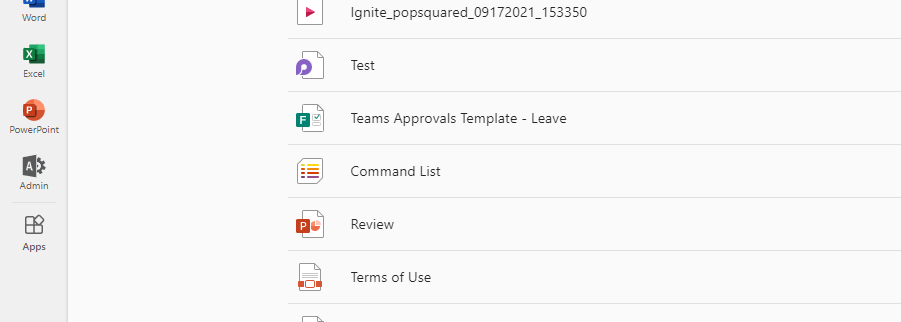
3.) In the M365 Admin Centre from the left navigation select Show All and then Azure Active Directory
4.) In Azure Active Directory, from the left navigation select Azure Active Directory
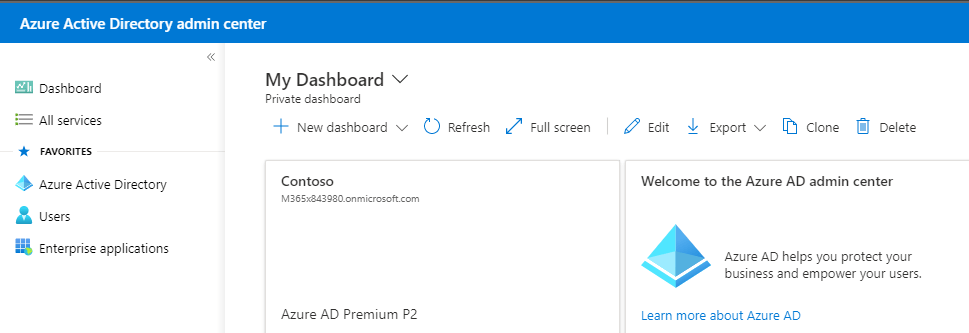
5.) Select Security
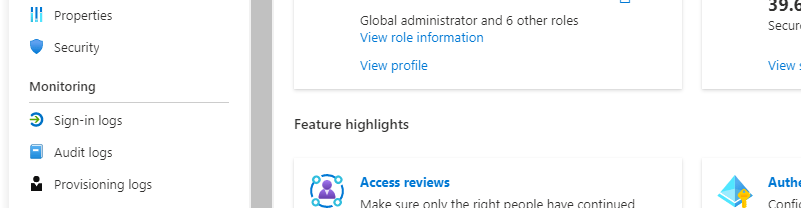
6.) Select Authentication Methods
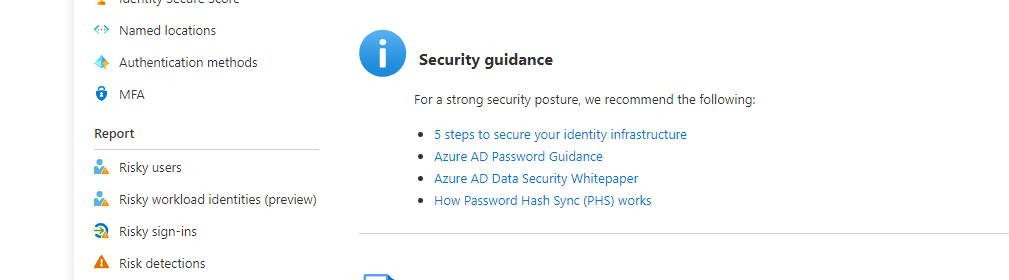
7.) Select Microsoft Authenticator
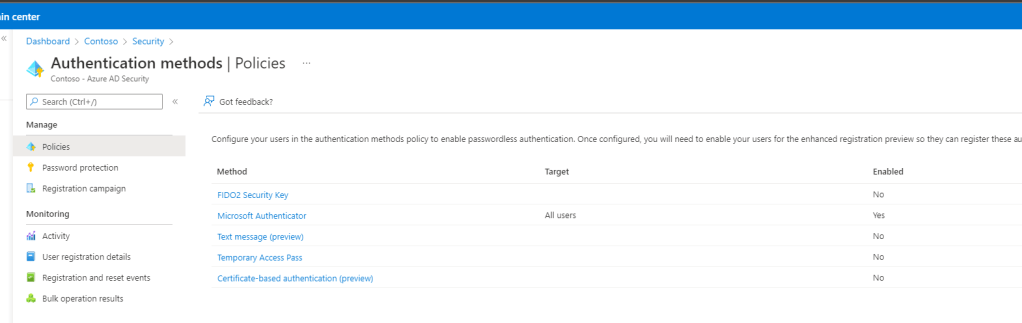
8.) Here, in this tenant, Microsoft Authenticator is enabled. If it isn’t enabled you can enable it at this point have users download the app and enrol. The target – who is permitted to use Microsoft Authenticator – is also to All Users which can be modified if only a user or group is required. This demo will stay with all users.
Select More Options (…) on the right and then select Configure
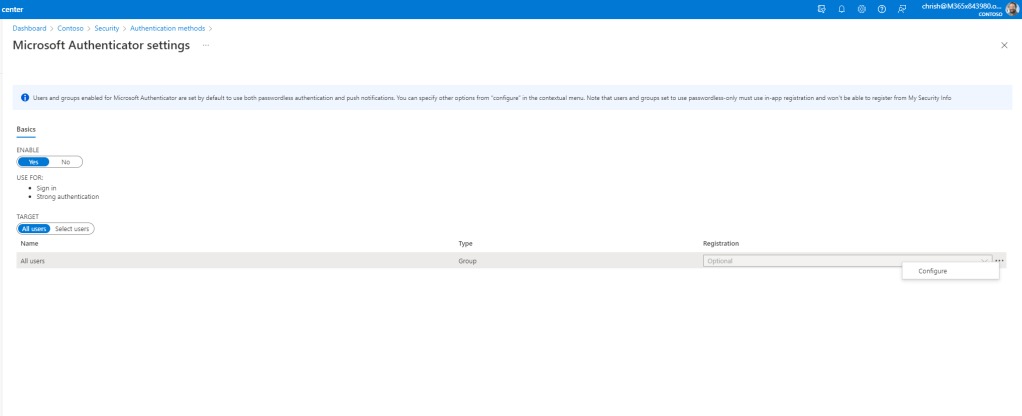
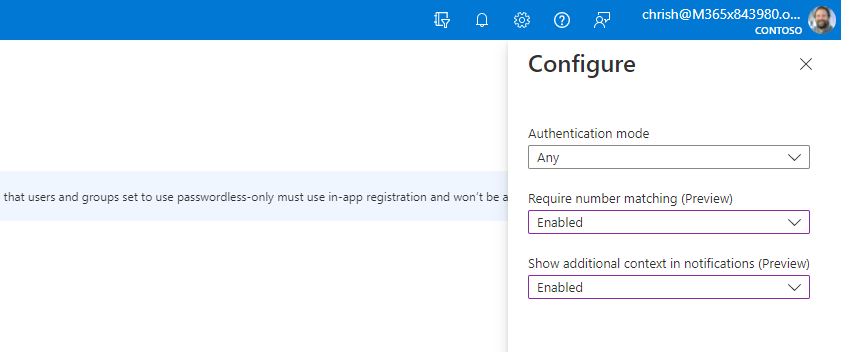
9.) In the flyout, change the options from Microsoft Managed to Enabled as in
Authentication Mode: Any
Require Number Matching: Enabled
Show Additional Context in Notifications: Enabled
Once done select Done
10.) Then select Save

11.) You should be notified that the policy was successfully saved
Our job is done. Let’s test this out.
ACCESSING TEAMS AFTER CONFIGURING AZURE AD
So in order to test this out I am going to access the Teams Web App experience
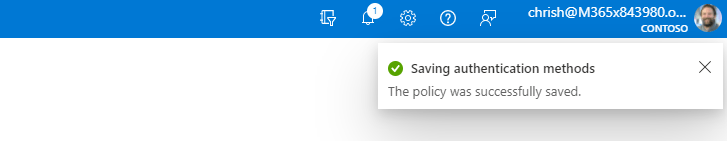
1.) In a fresh browser session I go to https://teams.microsoft.com

2.) Log in again with my credentials
3.) I now get a number I have to enter into Authenticator
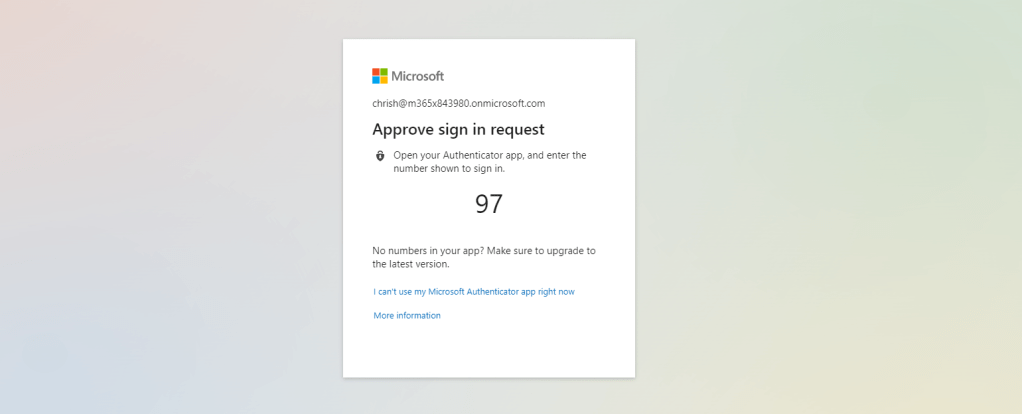
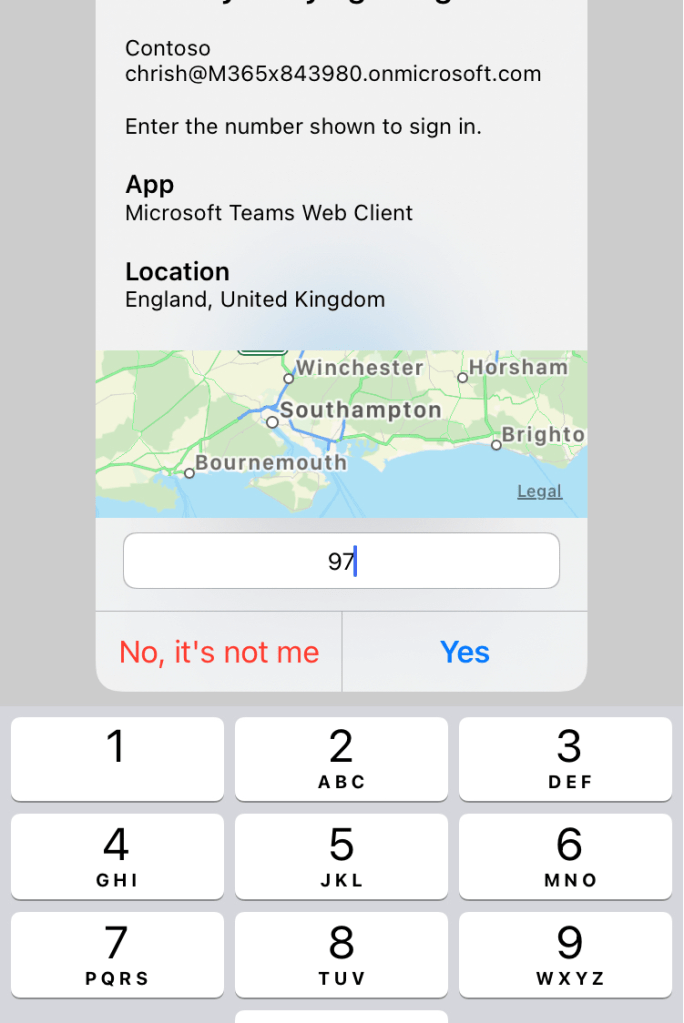
4.) I now open the authenticator app which shows far richer information. It shows the correct app I am actually trying to access – Teams. It shows my location and I have to Enter The Number provided and select Yes
5.) I am now into the Teams Web App

So easy and this has taken me less than 45 minutes to implement and write this blog end to end.
FAQ
Q. Why isn’t this turned on by default?
A. According to Microsoft number matching will be automatically turned on a few months after it has entered GA. At the time of writing, it’s still in preview. Regarding Additional Context there is nothing specified, however it would make sense to auto enable both these settings as the authentication experience is just so enhanced.
Q. Is there any limitations?
A. According to documentation both number matching and additional context can only be enabled for a single group. This is fine in an all users situation, or where there is a specific dynamic group to enable this on, however it may limit scenarios outside of this. Personally, these are functionalities I would enable on everyone
Q. Isn’t number matching part of Authenticator if you use Passwordless?
A. Yes, for those who have gone passwordless number matching is already part of the authentication experience so only additional context will be a new add


One thought on “[Archived] Teams Real Simple with Pictures: Adding Number Matching and Context to Authenticator Notifications via Azure Active Directory”
Comments are closed.