This blog is part of a series on Teams. For more articles, check back often.
Written: 15/09/2019 | Updated: N/A
Data Loss Prevention (DLP) is a strategy for ensuring that team members do not send sensitive or critical information outside of the corporate network or to other team members. This could include financial information, personally identifiable information (PII) such as credit card numbers or information pertaining to Intellectual Property (IP) such as the design for a new application. It could even be extended to use cases such as barring profanity to be used in communications. Whilst Teams is a powerful application for users to be able to communicate and collaborate with guests and with other users in other Teams tenants, organisations also need to protect themselves against data leakage and the infringement of compliance regulations such as GDPR. Applying a DLP Policy to Teams is an essential step in any Teams deployment
WHY WOULD WE DO IT?
- To prevent team members sending sensitive or critical information outside the network or to other team members
- To curb use of profanity or sensitive language in communications
- To prevent data leakage and infringement of compliance regulations
PREREQUISITES
The administrator will need a role which can amend DLP settings in the Office 365 Security & Compliance Centre, such as
- Security Administrator
- Compliance Administrator
- Compliance Data Administrator
- Organization Management
Or have
- Global Administrator
Data loss prevention capabilities were recently added to Microsoft Teams chat and channel messages for users licensed for Office 365 Advanced Compliance, which is available as a standalone option or included in Office/Microsoft 365 E5 Compliance
To cite Microsoft on the use of DLP
DLP with Chat/Messages: Suppose that someone attempts to share sensitive information in a Teams chat or channel with guests (external users). If you have a DLP policy defined to prevent this, messages with sensitive information that are sent to external users are deleted. This happens automatically, and within seconds, according to how your DLP policy is configured. DLP for external chat sessions will only work if both the sender and the receiver are in Teams Only mode and using Microsoft Teams native federation. DLP for Teams does not block messages in interop with Skype for Business or non-native federated chat sessions.
DLP with Files: Suppose that someone attempts to share a document with guests in a Microsoft Teams channel or chat, and the document contains sensitive information. If you have a DLP policy defined to prevent this, the document won’t open for those users. Note that in this case, your DLP policy must include SharePoint and OneDrive in order for protection to be in place. (This is an example of DLP for SharePoint that shows up in Microsoft Teams, and therefore requires that users are licensed for Office 365 DLP (included in Office 365 E3), but does not require users to be licensed for Office 365 Advanced Compliance.)
HOW
NOTE: This article will show you how to create a DLP policy with a custom sensitive information type. Microsoft 365 comes pre-populated with many sensitive information types which can simply be added when creating the DLP Policy, however, since most organisations use a mix of pre-populated and custom sensitive information types its important to know how to create custom ones too.
1.) Log into Microsoft 365 at https://login.microsoftonline.com
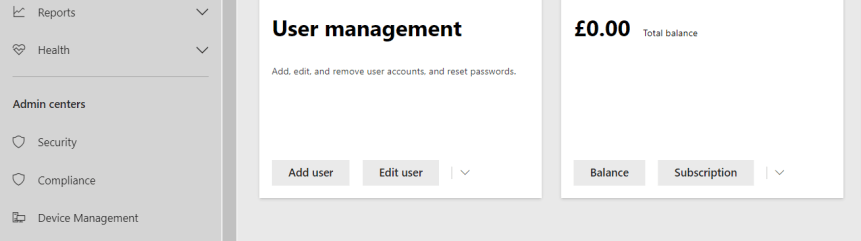
2.) Select Admin
3.) Under Admin Centres in the left navigation select Compliance
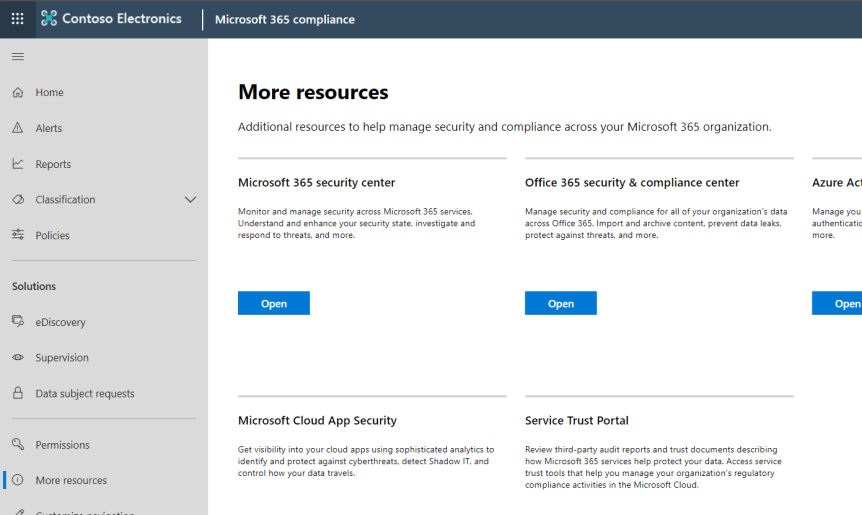
4.) Select More Resources in the left navigation. Under Office 365 Security & Compliance Centre select Open
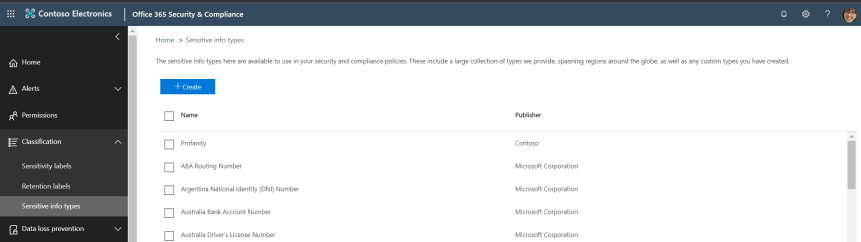
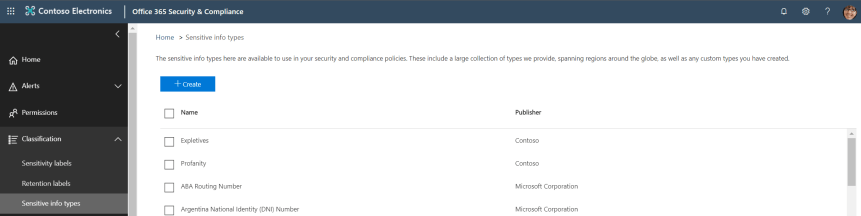
5.) Select Classification then Sensitive Info Types in the left navigation. Select Create
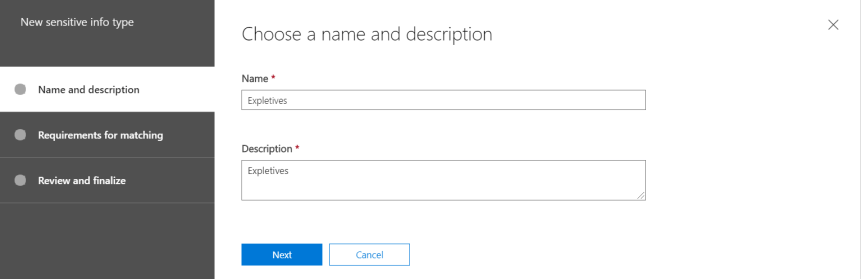
6.) Enter a Name and Description of the Sensitive Info Type. In this example we’ll use Expletives. Select Next
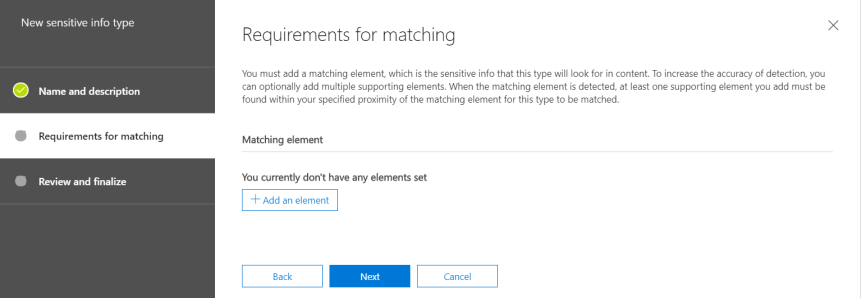
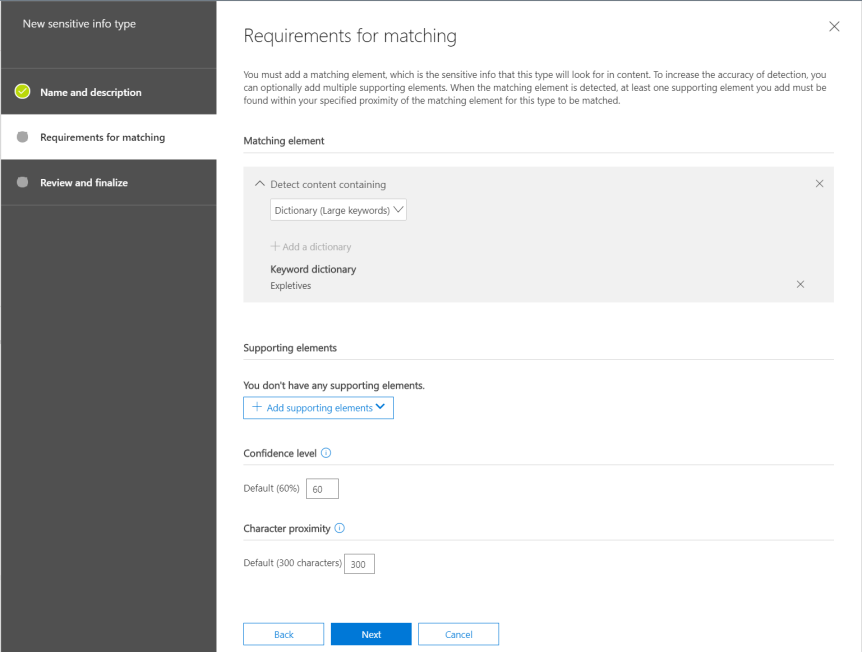
7.) Select Add an Element
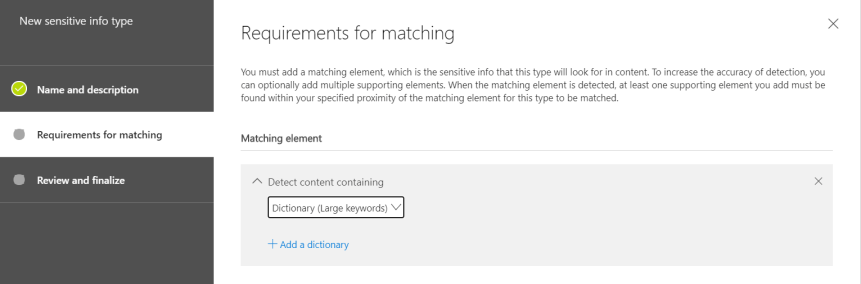
8.) Set Detect Content Containing to Dictionary (Large Keywords) and select Add a Dictionary
9.) If there are no pre-existing dictionaries present select You can create new keyword dictionaries here
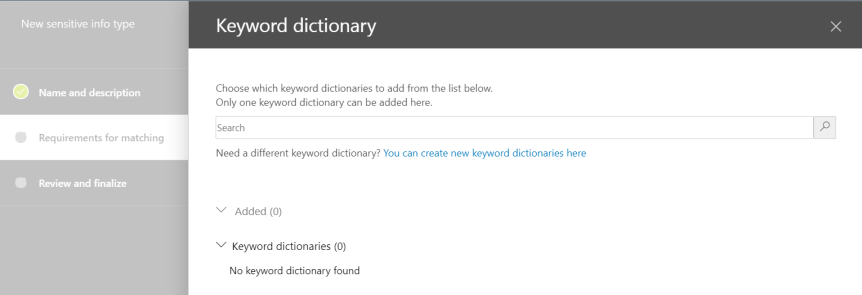
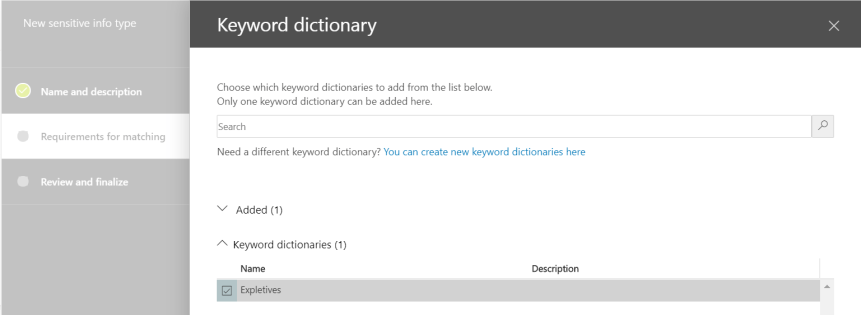
10.) Create the keyword dictionary and Save. Highlight the dictionary and then Add

11.) Select Next
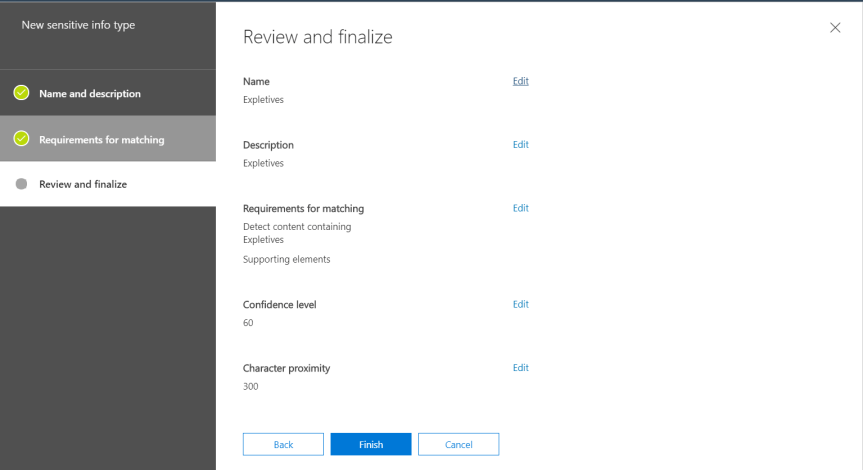
12.) Select Finish and check the sensitive info type has been created (as shown here by the creation of sensitive info type Expletives). At this point several other sensitive info types may be created such as Racist Language, Sexually Explicit Language if required
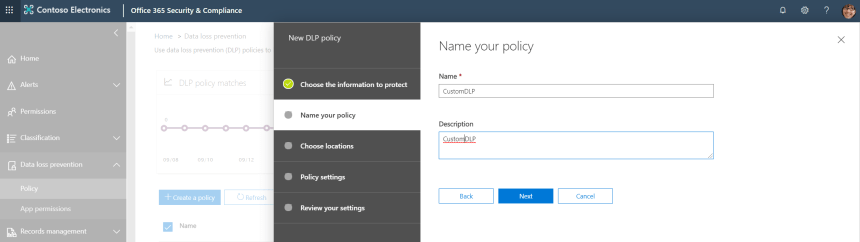
13.) Go to Data Loss Prevention in the left nav, then Policy, then select Create a Policy

14.) Choose predefined policies (as stated above) or choose a custom policy. For this article a custom policy will be chosen. Select Next

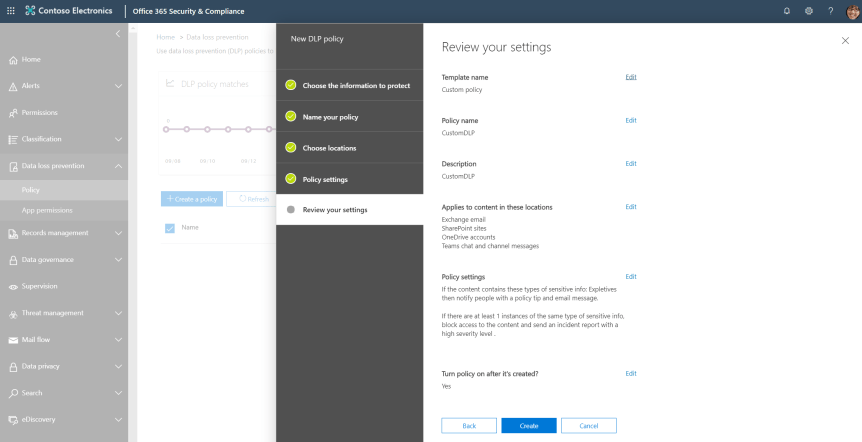
15.) Name the policy – here selected as CustomDLP. Select Next
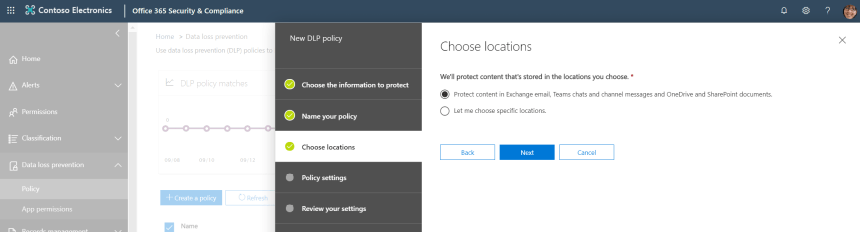
16.) Choose the locations to protect. The selections are a.) ‘Protect content in Exchange email, Teams chats and channel messages and OneDrive and SharePoint documents’ or b.) to choose specific locations. This example will choose a.) – however, the screenshot below for specific locations shows that users can be included/excluded from the policy. Once done, select Next

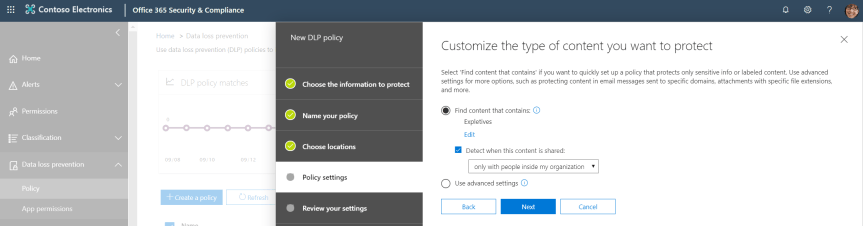
17.) Choose the content that is needed to be protected. Advanced Settings can be used to apply more complex rule sets to the DLP Policy (such as applying to specific domains). Select Edit to choose the content type.
Note: As outlined here on Petri, Teams communications are internal whilst DLP checking for other workloads focuses on outbound email/document sharing. The DLP policy must therefore cover content shared “only with people in my organization” (many existing policies are likely set to cover content shared “with people outside my organization.” In the context of Teams, this means teams with guest users). It is recommended – if external and guest access is on to set two DLP Policies – one internal and one external.

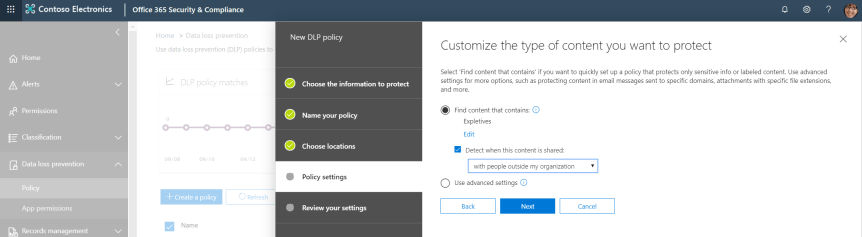
18.) Sensitive information types (as created above) or labels can now be applied. Select Add and Sensitive Info Types
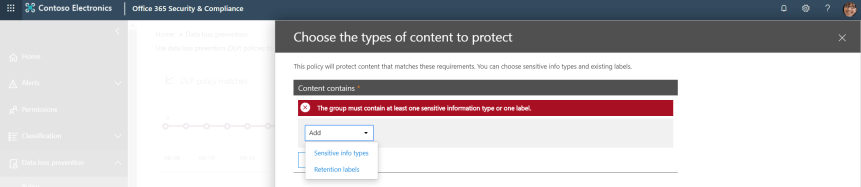
19.) Add the Sensitive Info Type (In this case Expletives) and select Done

20.) Select Save

21.) Select Next
22.) Set the actions which apply to the detection of sensitive info. This includes the setting of policy tips, the specific amount of info being shared, who the incident reports are sent to and the ability to block the share. Once complete, select Next

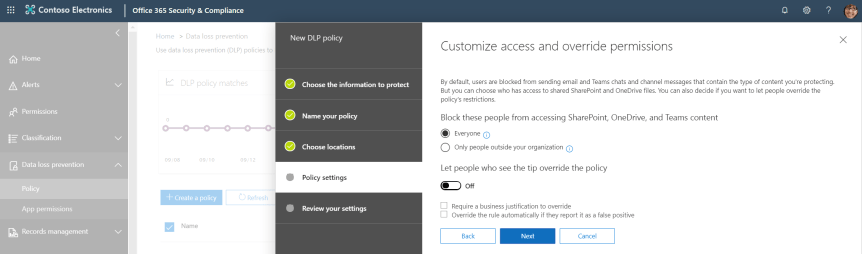
23.) Set the access and override permissions. As shown below, this policy has been used to block everyone and cannot be overridden. Select Next
24.) Choose whether to test the policy or apply it immediately. Best practice will usually be to test the policy first, however here it is being applied immediately. Select Next

25.) Once reviewed, select Create
Our job here is done.
Wait up to an one hour for the DLP Policy or policies to propagate through the system and then test out the policy in Teams to see if it is applied. Here shows both the block and the email being sent to the administrator once the Expletives policy has been applied


And with files (both for OneDrive and SharePoint)


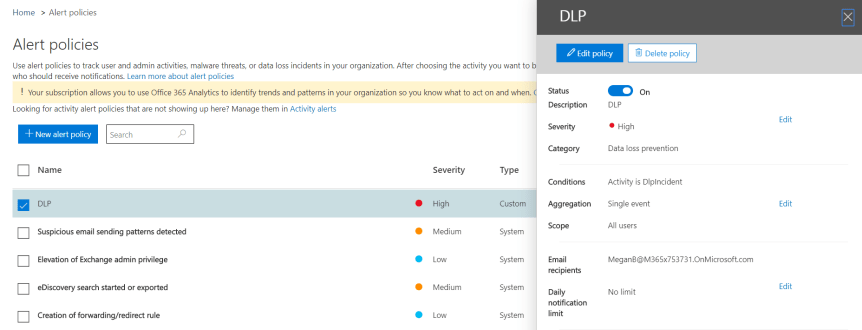
Additional alerting in the Office 365 Security and Compliance centre can be set up for DLP policy matches if required


3 thoughts on “Teams Real Simple with Pictures: Applying Data Loss Prevention (DLP) to Chat, Channel Messages and Files”
Comments are closed.