This blog is part of a series on Teams. For more articles, check back often.
Written: 10/12/2019 | Updated: N/A
We have previously explored the implementation of DLP and Supervision policies to the Team. We will now look at applying Sensitivity Labels – currently in Public Preview. By definition, Sensitively Labels allow Teams admins to regulate access to sensitive organizational content created during collaboration within teams. In other words, it can keep Teams private (removing the ability to be set as public), block Guests from being added and block the team being accessed from unmanaged devices. They can be set at a tenant level by the admin once the label has been created (via Azure) or easily applied when creating the Team by the owner. It gives administrators more control over their Teams in terms that users cannot simply join Teams and Owners cannot simply add guests which are not authorised to access it’s content. It’s another layer of protection which should be added in any Teams roll-out. It’s also an answer for blocking guest access on a Team by Team basis.
WHY WOULD WE DO IT?
- For regulating access to sensitive content
- For blocking guest access on a Team by Team basis
PREREQUISITES
Global administrator permissions to enable the preview, then a role (I.e. Security/Global Admin) which can create sensitivity labels in the Microsoft 365 Admin centre. Through prior testing it is also recommended that guest access is enabled in the Teams Admin Centre before attempting this. An Office/Microsoft 365 plan which contains Azure AD P1 licences are required.
HOW
This guide will assume that the Azure Powershell module is not installed and the preview has not been enabled. Also note this functionality is currently in public preview. If any bugs are experienced, please raise to Microsoft Support. To set expectations, once the sensitivity label has been published in a policy it could be 24 hours before teams with sensitivity labels are able to be created (in my case it was more like 36) – even after the sensitivity label appeared as an option when creating the Team.
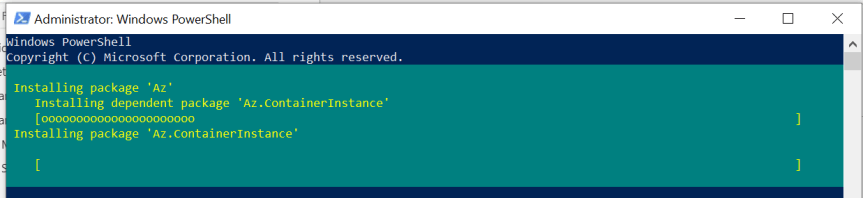
1.) Run Windows Powershell as Administrator

2.) Install the Azure Powershell Module using command
Install-Module -Name Az -AllowClobber -Scope CurrentUser

3.) Select Yes (Y) or Yes to All (A). The PS Gallery will be installed

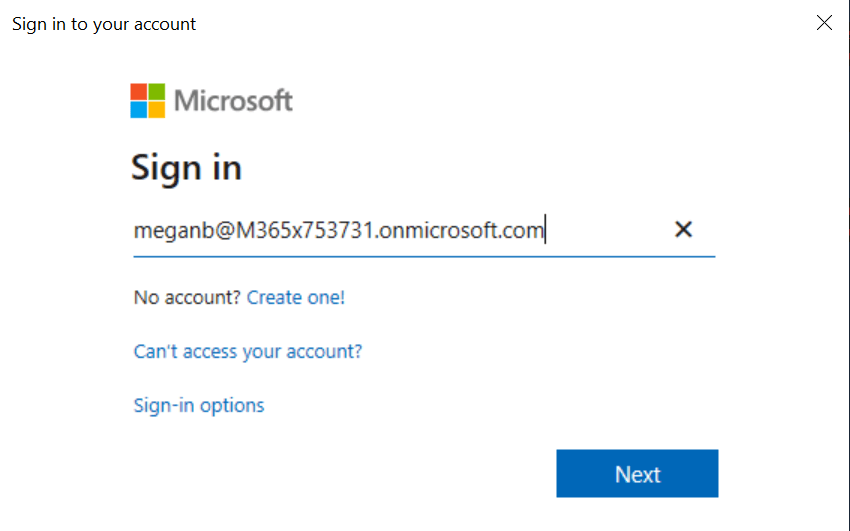
4.) Use Command Connect-AzAccount and connect with a Global Administrator account


5.) Run the following script (and sign in again) to enable the preview
Connect-AzureAD
$setting=(Get-AzureADDirectorySetting | where -Property DisplayName -Value “Group.Unified” -EQ)
if ($setting -eq $null)
{
$template = Get-AzureADDirectorySettingTemplate -Id 62375ab9-6b52-47ed-826b-58e47e0e304b
$setting = $template.CreateDirectorySetting()
$setting[“EnableMIPLabels”] = “True”
New-AzureADDirectorySetting -DirectorySetting $setting
}
{
$setting[“EnableMIPLabels”] = “True”
Set-AzureADDirectorySetting -Id $setting.Id -DirectorySetting $setting
}

6.) Successful execution will be confirmed

7.) Login to https://login.microsoftonline.com
8.) Select Admin

9.) Select Compliance from the left hand nav

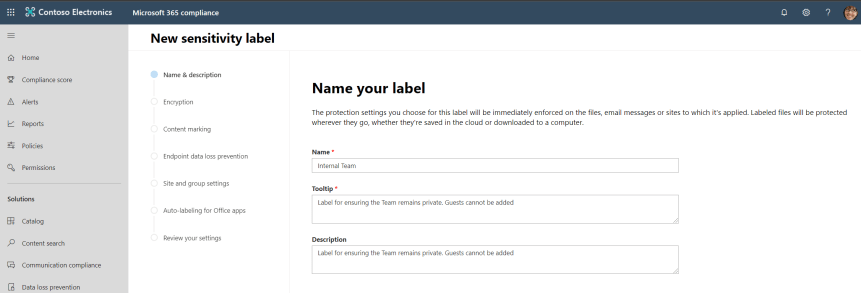
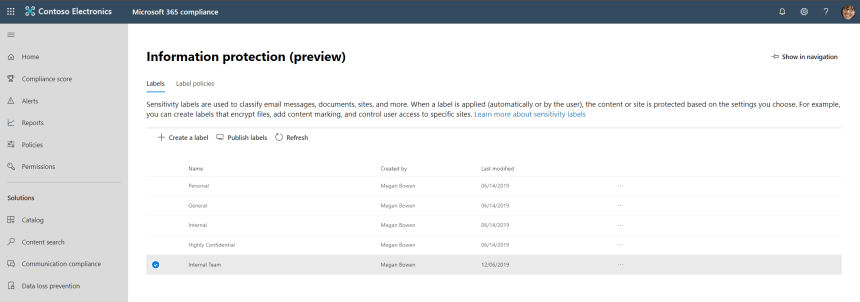
10.) Select Information Protection from the left hand nav, then Create a Label

11.) At this point, per supporting documentation, it’s important to note that only the site and group settings take effect when you apply a label to a team, group, or site. Other settings, such as encryption and content marking, aren’t applied to all content within the team, group, or site. If a label is created and site and group settings are not turned on, the label will still be available but it won’t do anything when users apply it
Enter the Name of the Team, the Tooltip and Description and select Next
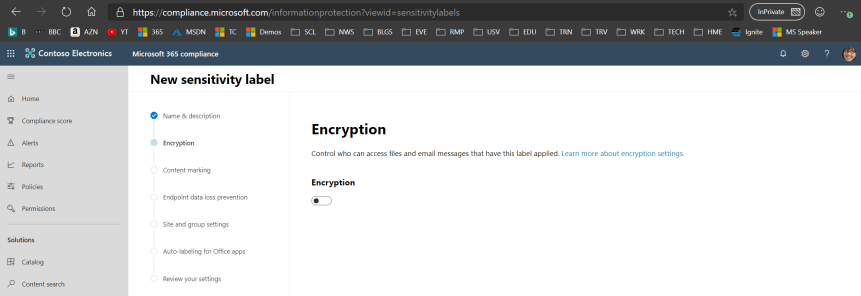
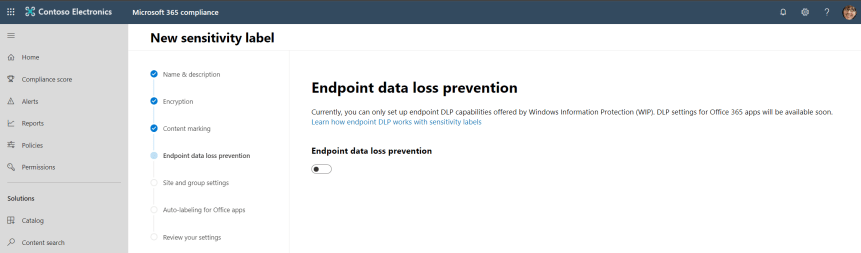
12.) Bypass Encryption, Content Marking and Endpoint DLP, selecting Next on each page

13.) On the Site and Group Settings page, turn on and set the privacy and uncheck that owners are allowed to add guests. The access policy for unmanaged devices can also be set.
- Privacy (Public/Private): Private means only approved members in your organization can see what’s inside the group. Anyone else in your organization can’t see what’s in the group
- Guest access: Control whether guests can be added to a group.
- Unmanaged devices: Block or limit access to SharePoint content from devices that aren’t hybrid AD joined or compliant in Intune. If you select Unmanaged devices, you need to go to Azure AD to finish setting up the policy.
Select Next

14.) Bypass Auto-labeling and on the review of the settings select Submit. The label is now created



15.) Select the label, then Publish Labels
16.) Select Next
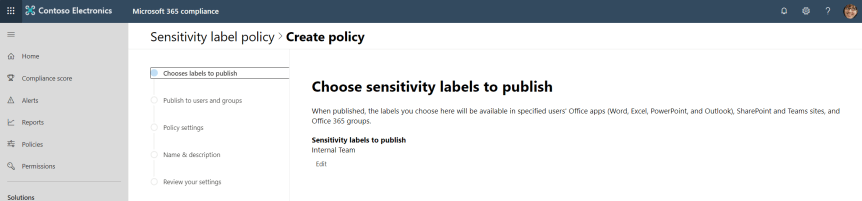
17.) Select the users or groups to publish to and select Next

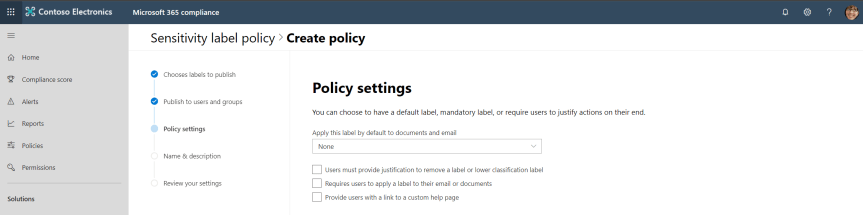
18.) Skip the policy settings and select Next
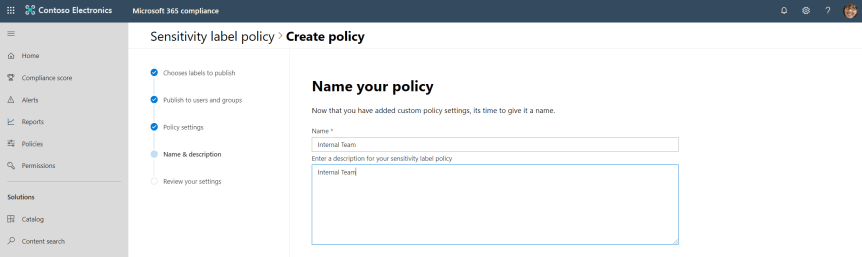
19.) Set a name for the policy, recommend as the same as the label, then select Next
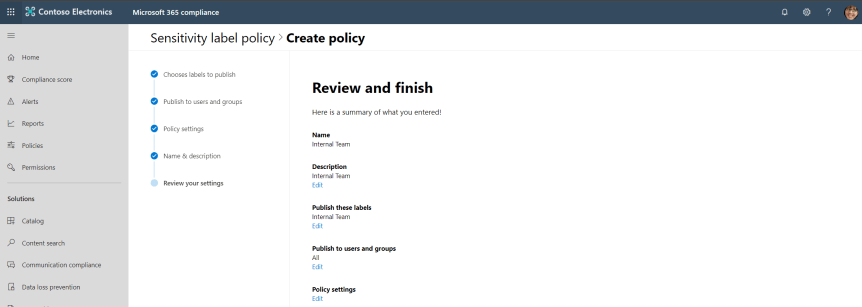
20.) Review and Submit. The label is now published with a label policy.

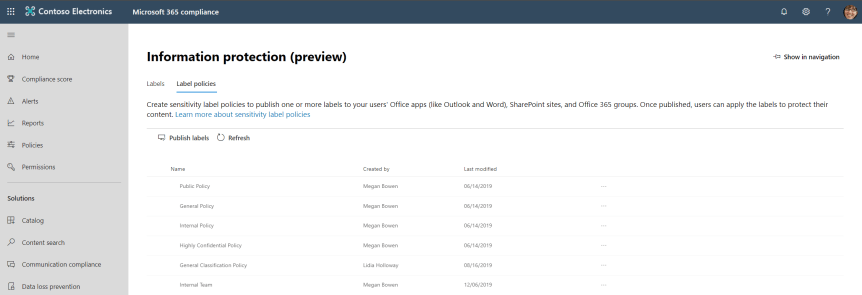
Our job here is done.
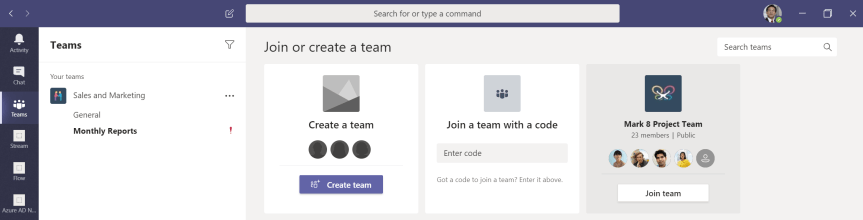
Once the propagation has completed (as said previously can take up to 24 hours and in my case more like 36) login as the user, select Join or Create a Team, Create a Team then Build a Team from Scratch


Select the created Sensitivity Label. Only a Private Team can be created


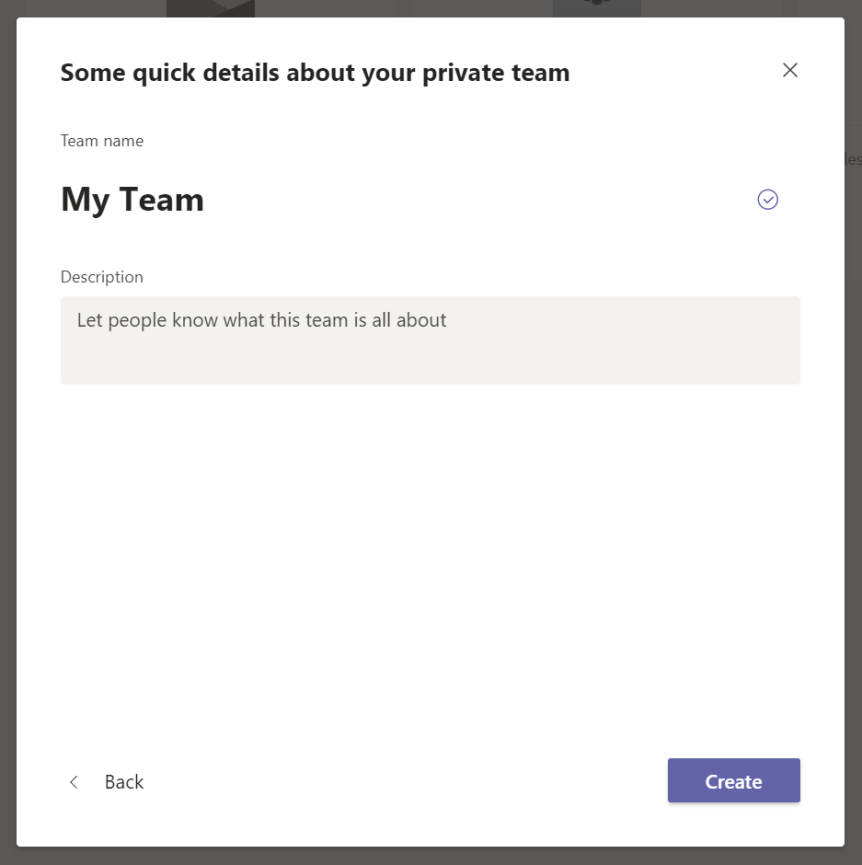
Once the Team is created, the label is visible on the Team

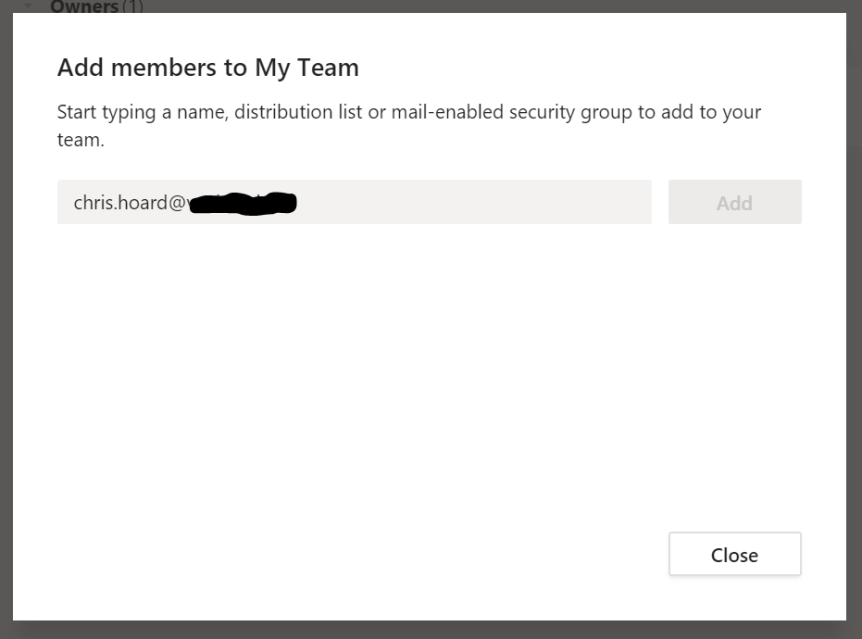
Guest add’s are grayed out and does not search externally whether trying to add through Add Members or through the Team Settings
All is showing as it should do in Azure AD

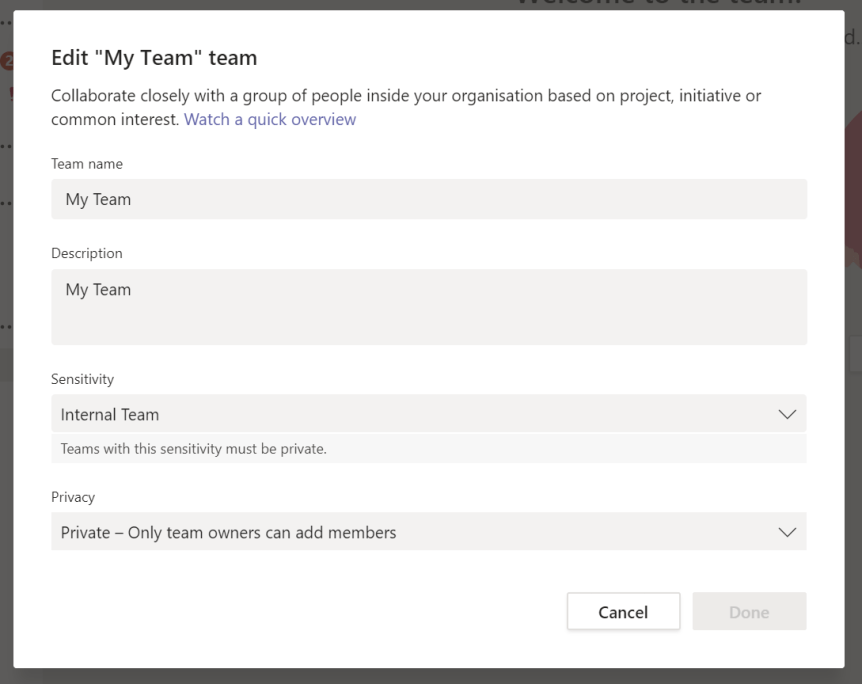
Sensitivity can be edited via Azure AD above or by Editing the Team. Again, to reiterate I would expect 24 hours or more for the change. Changes and removal of the label should show in the top right hand corner of the Team. In the case of removal this should return to the Org default.


AREAS OF DEVELOPMENT
As this is a public preview feature, it isn’t the finished article. Trying to anticipate what will probably be the biggest asks will be
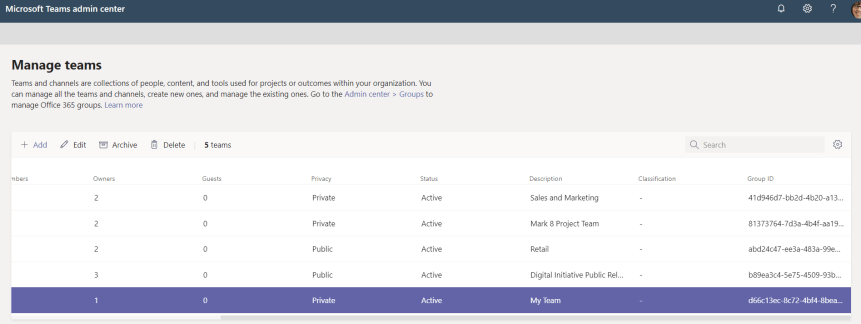
- Seeing the sensitivity in the Teams Admin Centre: Can only see classification so far, so would be good to see sensitivity here
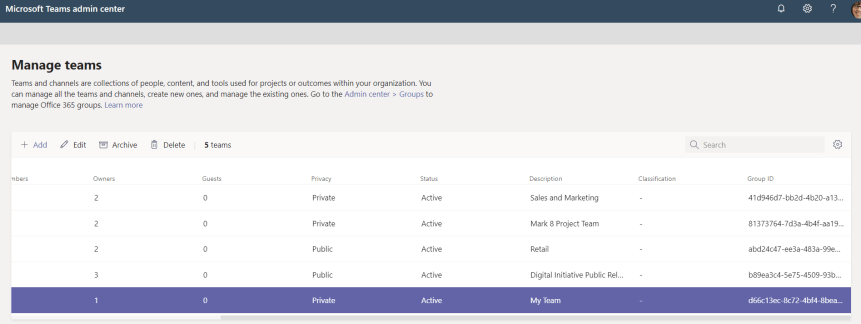
- Being able to filter sensitivities in the Teams Admin Centre: In addition to being able to see sensitivities being able to filter them if there are multiple labels
- Being able to report on Sensitivities: In the analytics

- Default Sensitivity in Teams Policies: Ability to set a default sensitivity


