This blog is part of a series on Teams. For more articles, check back often
Written: 05/12/2021 | Updated: N/A
Christmas has seemed to come around mega fast this year. It’s three weeks today. Hopefully, you’ve already done your shopping by now and have a week or two off to enjoy the festivities. I had some time today to sit down and watch Elf with my son. This’ll begin a marathon of Christmas movies which will include The Santa Clause, Miracle on 34th Street, Home Alone and my personal favorite It’s a Wonderful Life. I’m also pretty sure we’ll all see the time honored question-slash-poll go up on social – ‘Is Die Hard a Christmas movie?’ or gif’s of John McClane – ‘yippe ki yay mother…’. Of course, I hope it all goes well for you this year. One present which has arrived early for all us Microsoft Teams fans is End to End Encryption (E2EE). Announced at Ignite back in the spring, the public preview is finally here. However, before we suddenly break out the eggnog and get a bit rowdy on those calls we have to understand a few things right off the bat.
Number 1: It is only for 1:1 calls. No meetings. Not yet. Number 2: It is only for VOIP calls. No PSTN. That isn’t supported currently. Number 3: only real time media is encrypted end to end – in other words, only voice and video is encrypted at the source and decrypted at the destination without any nodes or parties decrypting/re-encrypting in between. Everything else – chat, files, presence, are encrypted but not end to end encrypted. Number 4: in an end to end encrypted call you can’t record, transfer, have captions or transcript, nor call merge, or transfer to another device or escalate the call. It’s literally a bare bones VOIP call designed for private communications which is a bummer if your organisation has compliant call recording needs. Number 5: It is not managed in the TAC yet. It has to be configured in PowerShell meaning you’ll need to keep a tight reign on who has it and who doesn’t. Number 6: E2EE isn’t enabled even after enabling it with PowerShell. Both ends need to enable it in their client settings. Number 7: Its only available in the desktop app and the mobile app. It’s not currently supported in web. So whilst this all sounds like a downer, actually it’s a sensible phasing out and it has been confirmed it a.) Works for federated calls given both parties have the policy enabled and b.) Works with guests
Let’s go
This blog will cover
- Enabling Public Preview
- Creating an E2EE Policy with PowerShell
- Enabling E2EE in Teams
- Did it work?
- FAQ
Note this blog may have some abridged steps which will assume some experience with a Microsoft 365 environment, particularly Teams and the Microsoft 365 Admin Centre
Prerequisites
- Microsoft 365 Licence which includes Teams
- Users who want to use E2EE should be enabled for Public Preview
- Global Admin/Teams Service Administrator permissions for PowerShell
ENABLING PUBLIC PREVIEW
1.) Log into https://login.microsoftonline.com
2.) From the left rail, or from the waffle, select Admin
3.) In the Microsoft 365 Admin Centre, select Show All and then select Teams
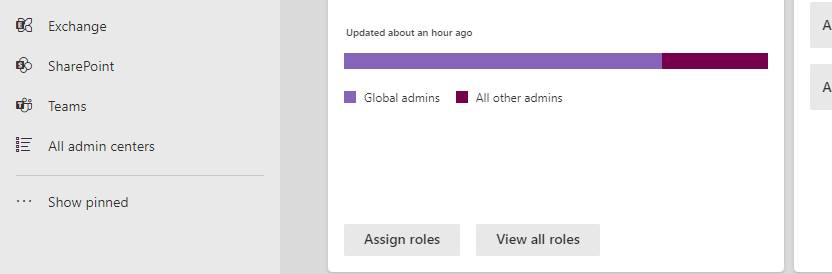
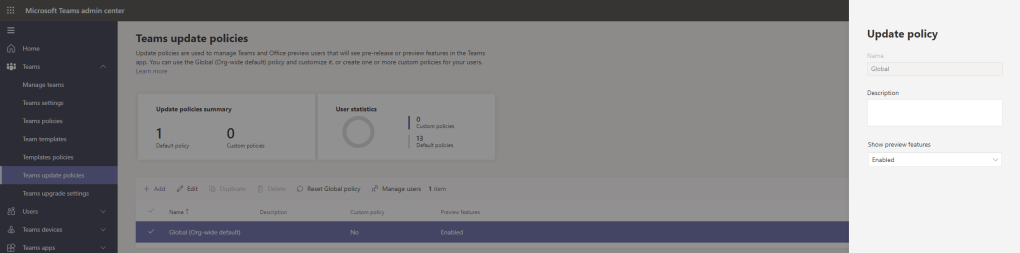
4.) Select Teams, then Teams Update Policies. If you want to enable for all users ensure Show Preview Features is set to Enabled in the global org wide policy. If you want to enable for some users, ensure you create a custom policy, again, with Show Preview Features is set to Enabled
5.) After a few hours of the policy being set, have the users log out and log back in again to Teams. Get them to select More Options (…) next to the avatar, then About then Public Preview. Have all users who will use E2EE do this
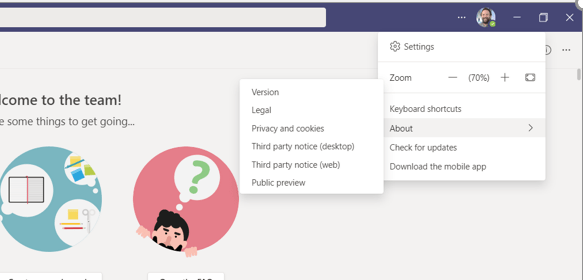
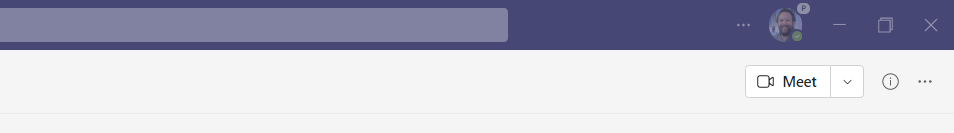
6.) Successfully being in Public Preview the avatar will be marked with a P
CREATING AN E2EE POLICY WITH POWERSHELL
Ok. So at this point the users that we want to use E2EE have been set up and enabled for the public preview. However, nothing has been applied yet. Let’s create the E2EE policy which is only possible at this time via PowerShell
1.) Search for PowerShell and then Run as Administrator
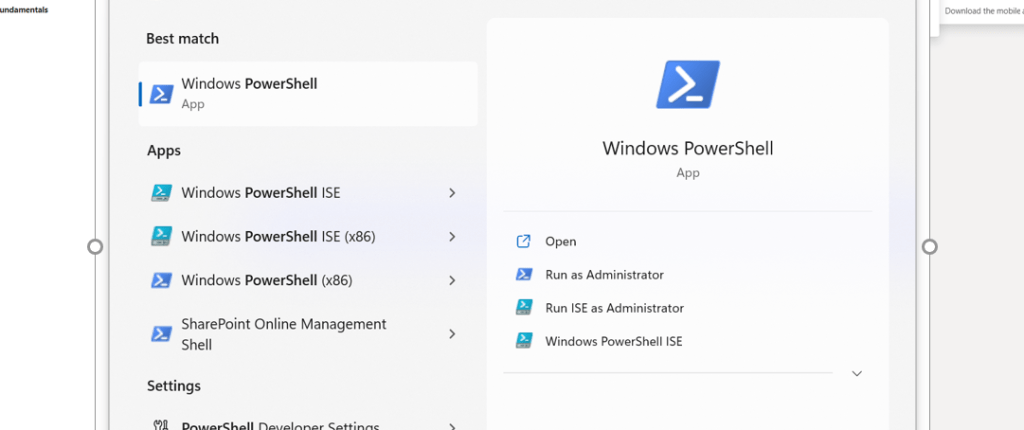
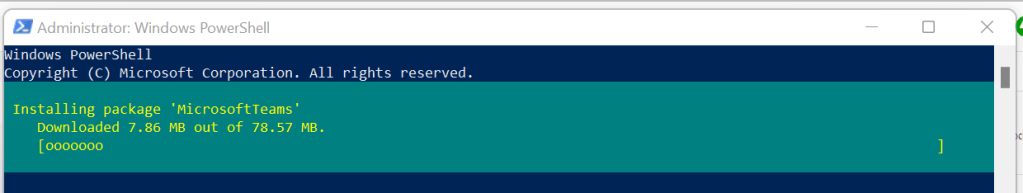
2.) This will assume that no Teams PowerShell module is installed. Run the following and the module will download and install
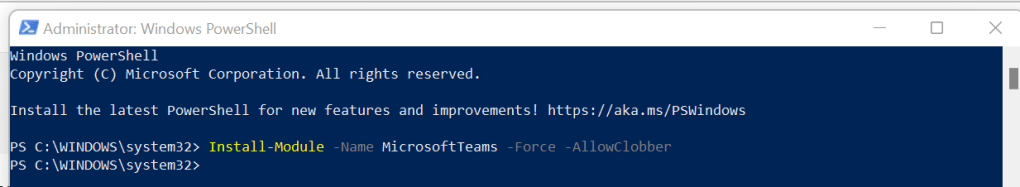
Install-Module -Name MicrosoftTeams -Force -AllowClobber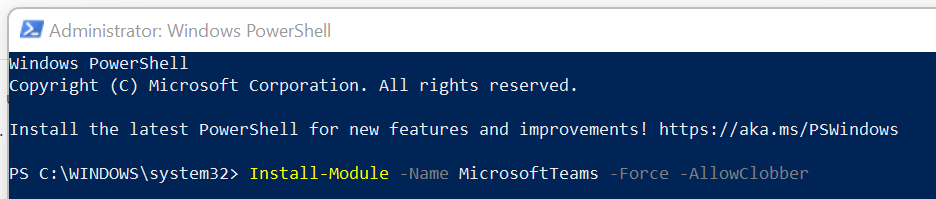
3.) Sign in using Global Admin credentials
Connect-MicrosoftTeams
4.) We are now ready to create a new E2EE Policy. Use the following as shown below. New-CsTeamsEnhancedEncryptionPolicy is the command to create a new policy. -Identity is the name of the policy. This has been called ‘E2EEPolicy’ in this example. The third command determines whether the E2EE functionality is available for the user or not. The two options are DisabledUserOverride which allows users to turn it on in the teams client, or Disabled, which disables the functionality and hides it in the Team client. Important Note. This is simply to create a policy, it will not be assigned to users until the next step
New-CsTeamsEnhancedEncryptionPolicy -Identity E2EEPolicy - CallingEndtoEndEncryptionEnabledType DisabledUserOverride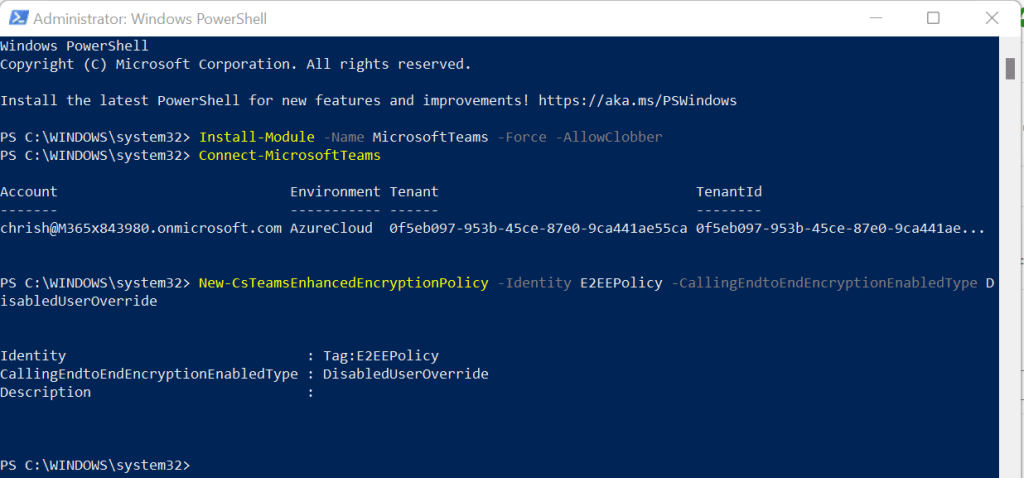
5.) Now the policy is created we need to assign it to some users. For this we’ll use the grant command. Rinse and repeat this for as many users as you need
Grant-CsTeamsEnhancedEncryptionPolicy -Identity 'chrish@M365x843980.onmicrosoft.com' -PolicyName 'E2EEPolicy'
6.) That’s it! The E2EE policy has now been set up and applied to your users
ENABLING E2EE IN TEAMS
Now that the policy has been set up and applied, users will need to go light it up in Teams. The recommendation here is that when the policy has been applied by the admin the users log out and back into Teams so the E2EE settings show.
1.) In Teams select More Options (…) next to the avatar, then select Settings

2.) Select Privacy
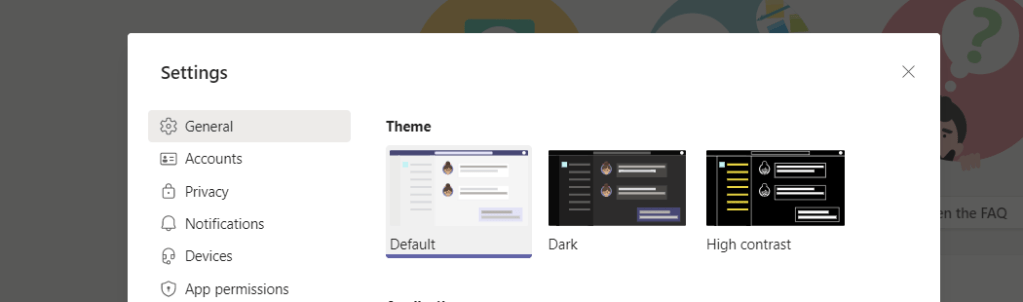
3.) The E2EE Option is now appearing. Swipe it on
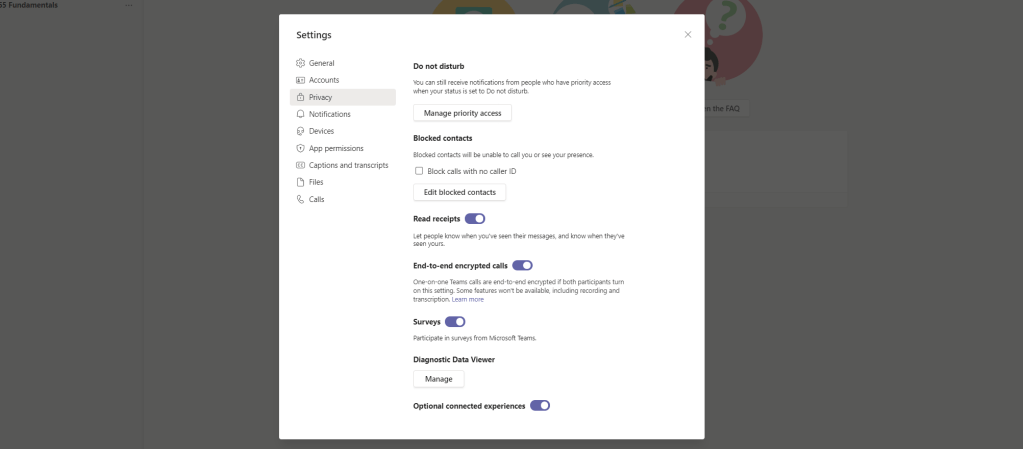
4.) Remember, for a 1:1 call to be E2EE, both parties need to have the policy applied and this setting enabled.
DID IT WORK?
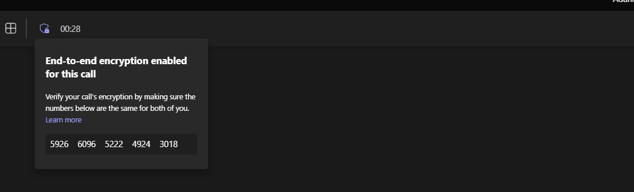
Yes, it did. Here is a call between Chris and Adam, two users who had the policy applied and who enabled E2EE in their settings. To check that E2EE has been applied successfully check the Shield with the Padlock Icon next to the view switcher and that the 20 Digit Number is the same for both calling parties
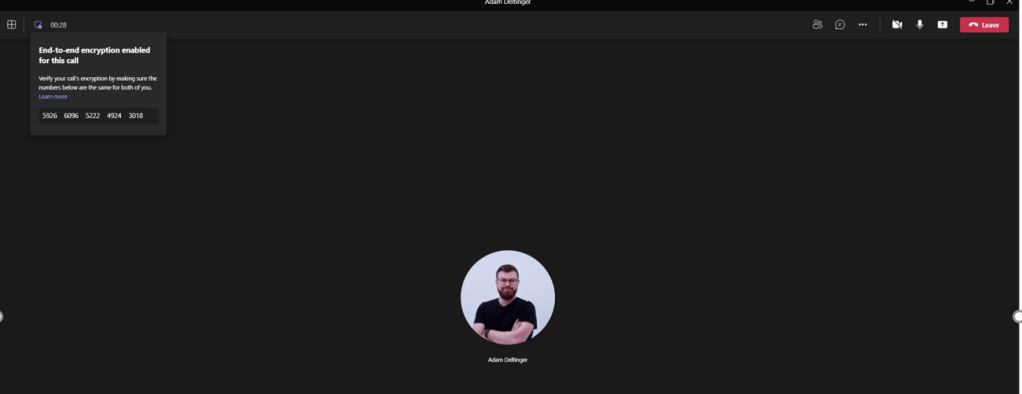
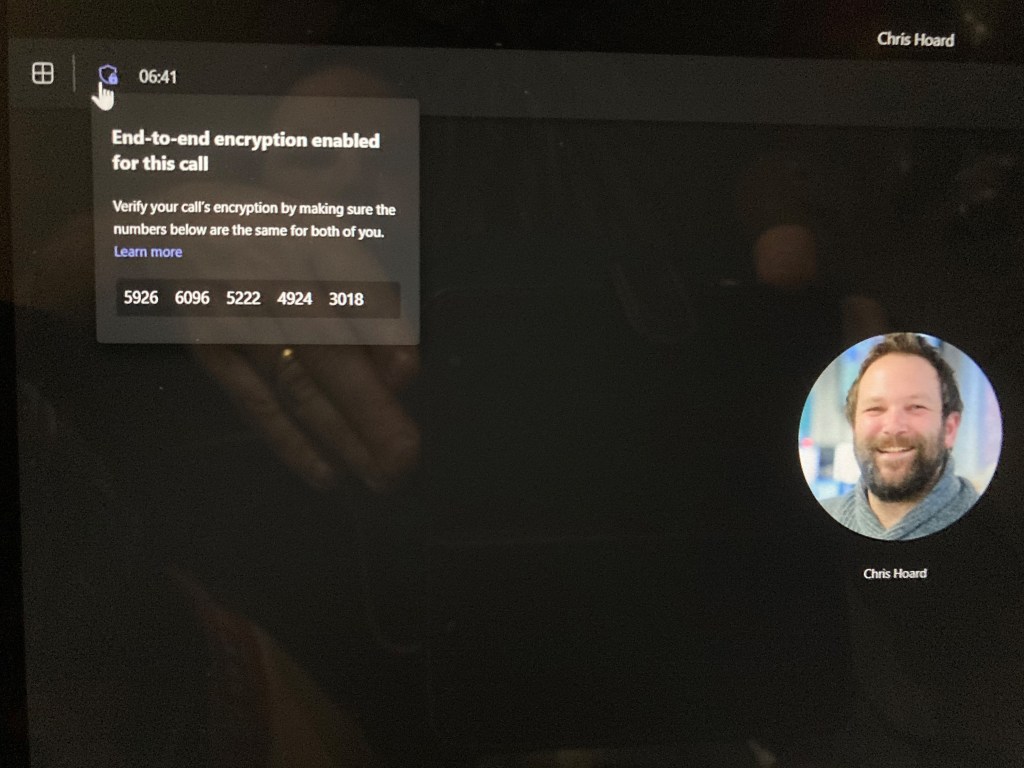
Our job here is done. EE2E applied to a VOIP call for two people in the org. As mentioned above this will work for federated orgs assuming the policies are applied and E2EE has been enabled on both ends. Looking forward to when this will roll out to more scenarios such as meetings, as well as PSTN calls.
FAQ
Q. Can EE2E be applied to the whole org?
A. Yes, using this for the global org wide policy
Set-CsTeamsEnhancedEncryptionPolicy -Identity Global -CallingEndtoEndEncryptionEnabledType DisabledUserOverrideQ. The example above was a custom policy?
A. Yes, the example above creating a new policy was a custom policy just in the same way you would create a custom messaging or meeting policy. This would probably be used more than just giving EE2E to the whole org
Q. You set up the policy and applied to users, but how to remove it from a particular user?
A. Use $NULL
Grant-CsTeamsEnhancedEncryptionPolicy -Identity 'chrish@M365x843980.onmicrosoft.com' -PolicyName $NULLQ. How do I get information on my E2EE Policies?
In PowerShell, custom policies are the ones with Tag:
Get-CsTeamsEnhancedEncryptionPolicy
Q. How do I see what EE2E policy a user has applied?
A. In PowerShell, run this. The Encryption Policy for the user will show here
Get-CsUserPolicyAssignment -Identity 'chrish@M365x843980.onmicrosoft.com'


One thought on “Teams Real Simple with Pictures: Let’s deploy End to End Encryption (E2EE) for 1 to 1 VOIP Calls”
Comments are closed.