This blog is part of a series on Teams. For more articles, check back often
Written: 19/12/2021 | Updated: N/A
It’s nearly here. The big day. My 5 year old is still building his Christmas list and wanting half of the things he sees on TV. It’s fingers crossed that the turkey will still be there when we go to pick it up at Mark’s and Spencer’s on Thursday. And of course we all hope that we’ll get to see our loved ones over the festive season given what’s happening with Omicron here in the UK. But for now, let’s put all the worries aside and focus on something we can control and do something about pretty quickly: which is implementing Safe Links for Microsoft Teams. It’s something easy to do, and the security benefits are 101. It’s all about protecting users from clicking on malicious URL’s directing them to sites aiming to instigate a data breach, or triggering the download of a payload onto their device. Given that Teams has open federation by default its pretty much a no brainer. I tend to think of it this way: what if someone who you regularly chat with in private from another organisation sends a link which you don’t recognise? How do you know that person hasn’t been breached? So how do you respond to someone you don’t know? What if someone who has been breached within your organisation sends you a document link within Teams with a malicious URL inside of it which to all extents looks like a legitimate business document? Now, I would love to say that everyone I know – myself included – exercises good judgement in these matters one hundred percent of the time. However, let’s be honest this just isn’t true. This is why zero trust is so important to everything we do moving forward. Chances are, someone will click the link. And it’s not because they are stupid. It’s often because they are busy, or under pressure, or the attackers are very good at making the URL look legit. How many of us ask somebody to ratify a URL before clicking on it? It could be a combination of those things and it could happen to any of us. Safe Links is included in Defender for Office 365 Plan 1. It’s in E5 but also a standalone SKU which could be added, for example to Microsoft 365 Business Premium. It’s important to note that everyone who you intend to protect with this needs to be licensed. If the licence isn’t on, it won’t work even if you add the user to the policy.
The application of Safe Links with Built in Policies, which is a new functionality now rolling into Preview, will be discussed in the next blog separately.
Let’s go.
This blog will cover
- Setting up a Safe Links Policy for Teams
- Applying via PowerShell
- Links within Attachments
- How to modify a Safe Links Policy Precedence
- Reporting on Teams Safe Links
Note this blog may have some abridged steps which will assume some experience with a Microsoft 365 environment, particularly Teams and the Microsoft 365 Defender Portal (Security Centre)
Prerequisites
- Microsoft 365 Licence which includes Teams, Defender for Office 365 Plan 1
- Permissions which can access the Microsoft 365 Defender Portal (E.g., Global Administrator) as well as configure Safe Links and Safe Attachment Policies
SETTING UP A SAFE LINKS POLICY FOR TEAMS
1.) Login to https://login.microsoftonline.com with admin credentials
2.) From the waffle, or from the left app rail, select Admin
3.) In the Microsoft 365 admin centre, from the left navigation, select Show All and then Security
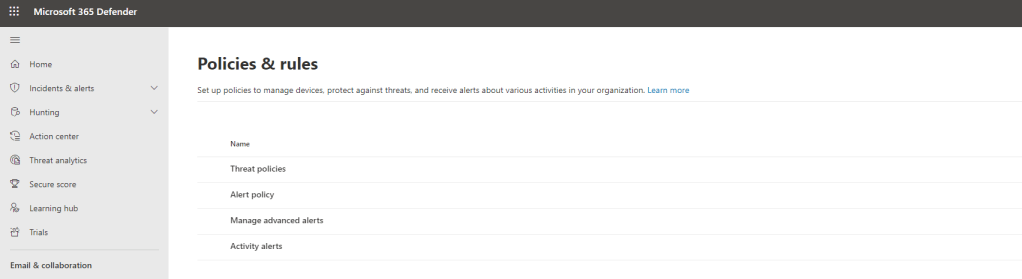
4.) In the Microsoft 365 Defender Portal, from the left navigation, select Policies & Rules
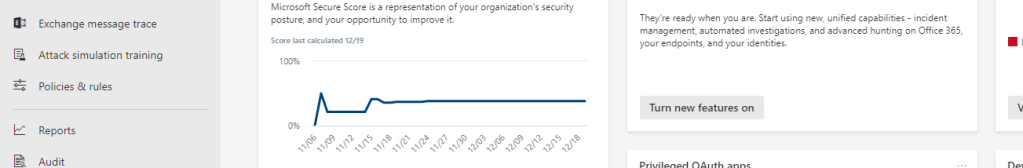
5.) Select Threat Policies
6.) Under policies select Safe Links
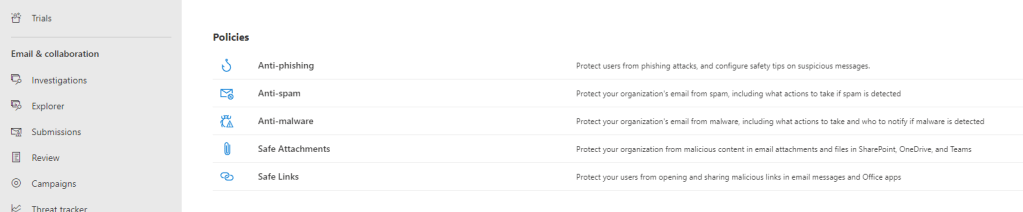
7.) By default, no policy has been created. Select Create

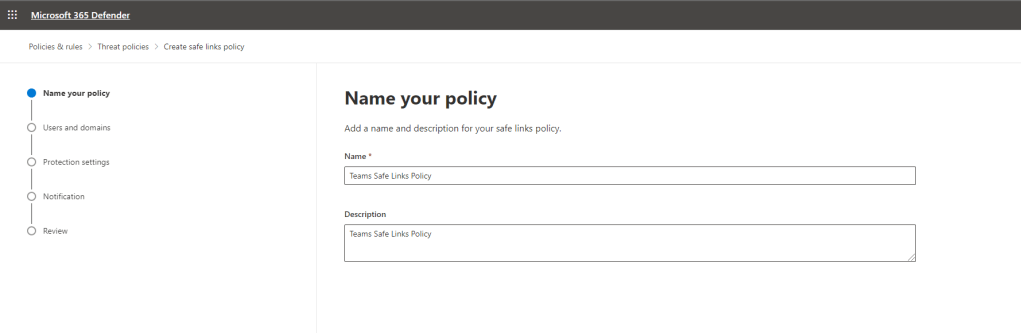
8.) Give your policy a name (Here shown as Teams Safe Links Policy). Select Next
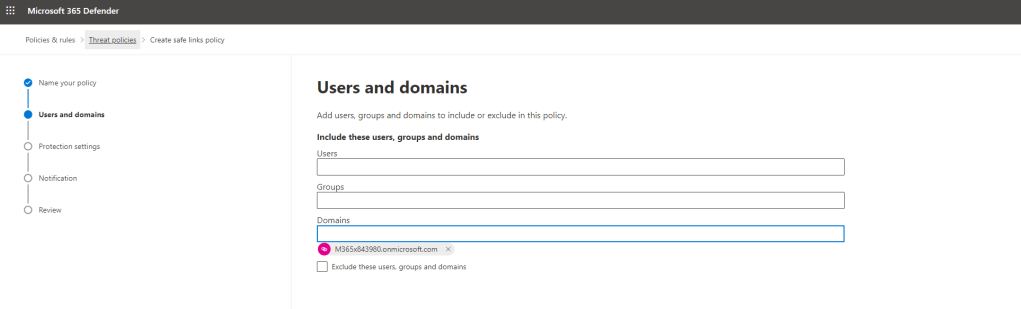
9.) Define the scope that the policy will cover – users, groups or domains. Exclusions can also be added via the checkbox. In this example, the policy will cover all the users in the organisation so the domain has been added. Select Next
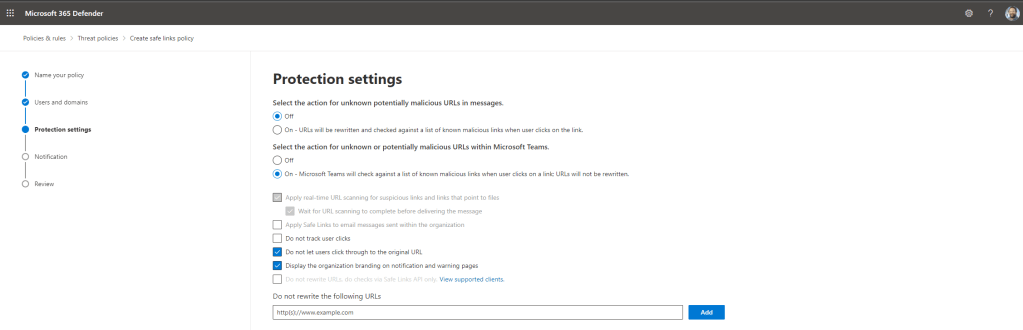
10.) In the protection settings, set Select the action for unknown or potentially malicious URL’s within Microsoft Teams to On. This will light up Do Not Track User Clicks which is recommended to be left unchecked as you will likely want to track for auditing purposed. It also lights up Do not let users click through to the original URL which is recommended to be checked (On) as this will reduce the risk of a security incident occurring. Finally, it also lights up Display the organisations branding which is also recommended to be checked since attackers use the Microsoft warning pages in attacks and so they need to be easily identifiable. Once done select Next
You will notice from the screenshot below that Select the Action for unknown potentially malicious URL’s in Messages is off. This is for Exchange, not Teams. Typically, you would probably have this on too as the single policy would cover Exchange and Teams. In this demonstration, this policy will only apply to Teams chats and conversations, not email.
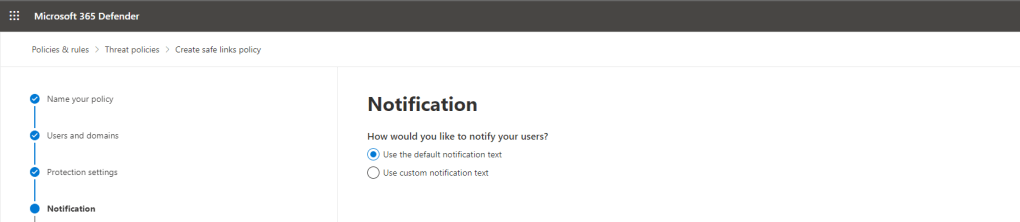
11.) Select the notification which can be default or custom. This leverages the default. Select Next
12.) Review the policy and select Submit
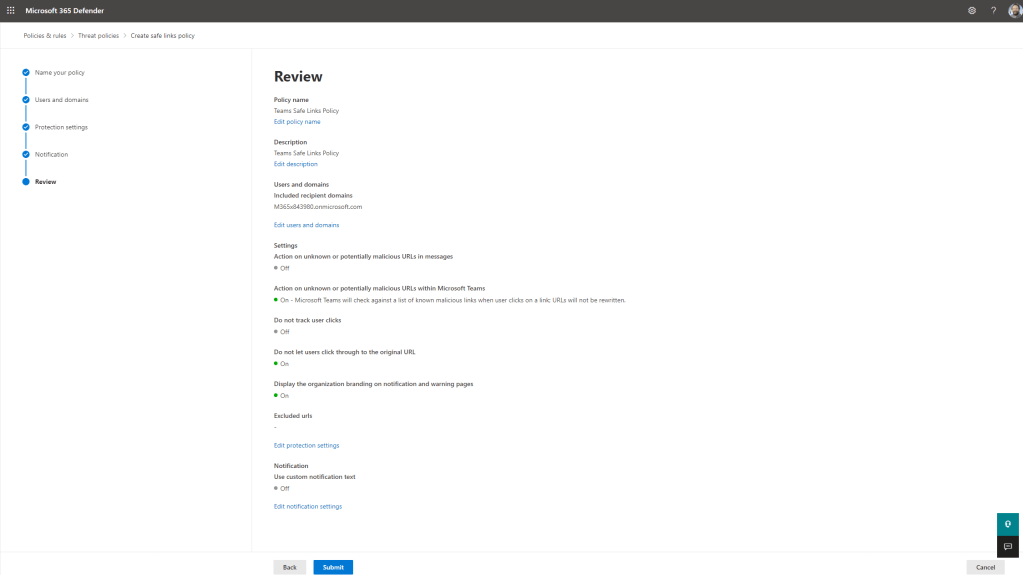
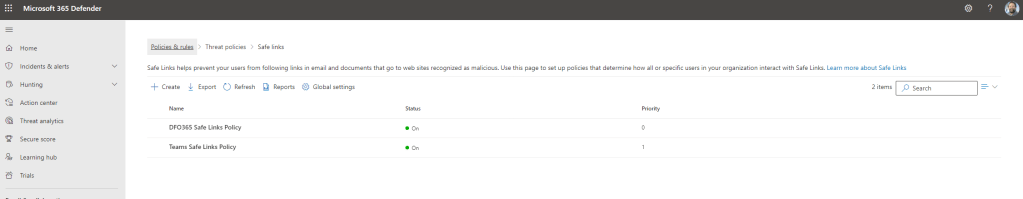
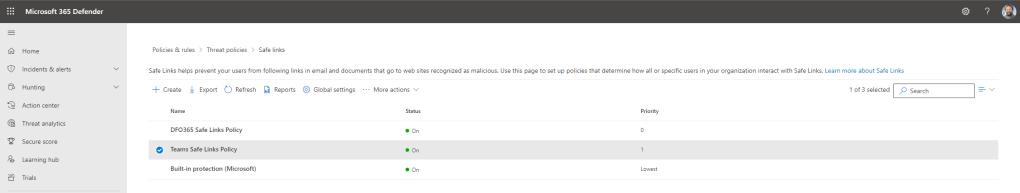
13.) The policy is now created and is added to any other policies created. How a policy priority is modified is shown later in this blog

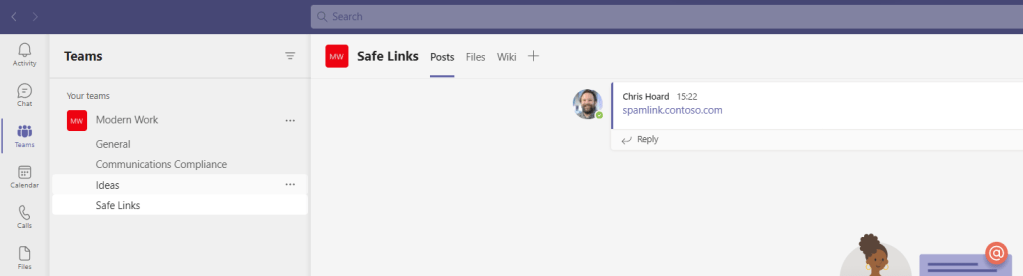
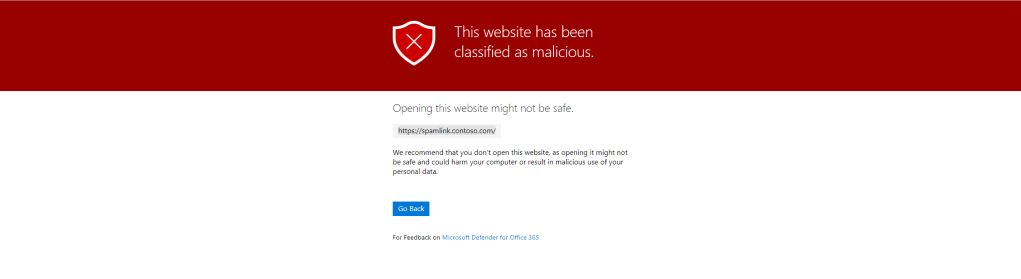
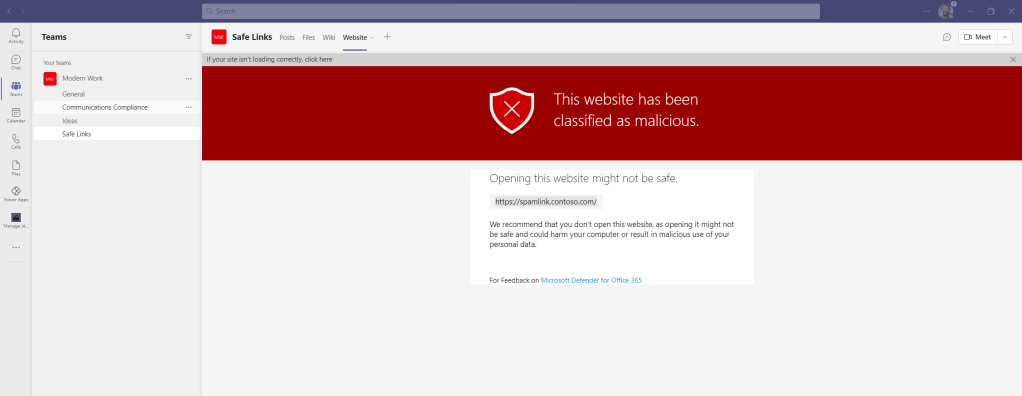
14.) Wait for the propagation of the policy (experience shows around 24 hours) and test. Clicking on a malicious link in a channel conversation will take you out to your default browser and will show the blocking page
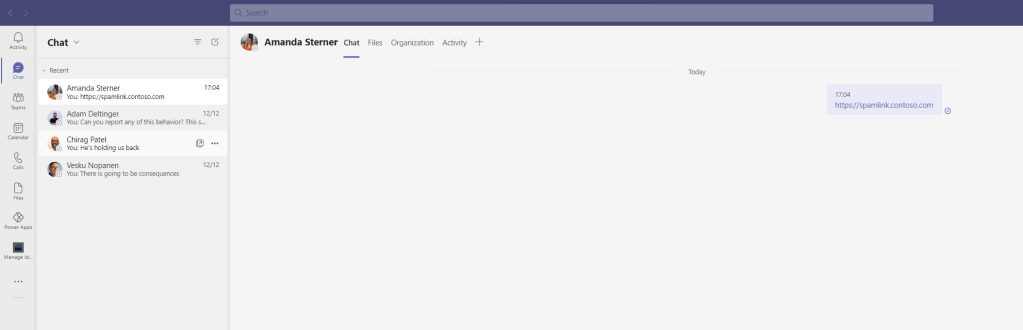
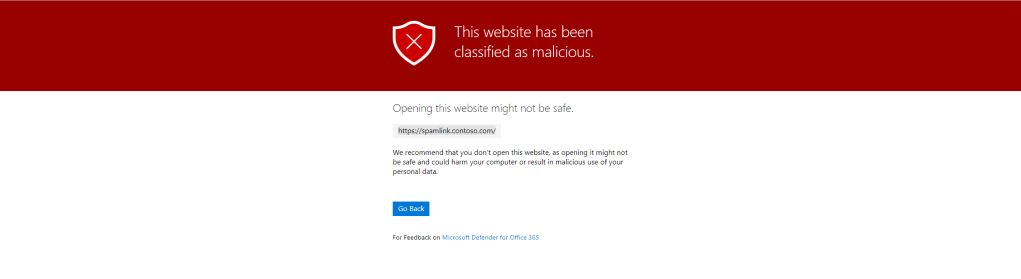
15.) Same with a private chat
16.) If the malicious URL has been used in a Tab, the block page will be shown in the Teams client
Our job here is done.
It is easy to implement a Safe Links policy for Microsoft Teams. It is something that we can do in less than 15 minutes and probably takes longer to configure the licencing.
APPLYING VIA POWERSHELL
We can also create the policy via PowerShell. This requires installation of the Exchange Online PowerShell V2 Module. Everything you have seen above in the GUI can be achieved in two commands
New-SafeLinksPolicy -Name "Teams Safe Links Policy" -EnableSafeLinksForTeams $true -DoNotTrackUserClicks $false -DoNotAllowClickThrough $true -EnableOrganizationBranding $trueNew-SafeLinksRule -Name "Teams Safe Links Policy Rule" -SafeLinksPolicy "Teams Safe Links Policy" -RecipientDomainIs [org].onmicrosoft.comNote, in the first command -DoNotTrackUserClicks and -DoNotAllowClickThrough even have to be specified as false/true are the default values when creating the policies
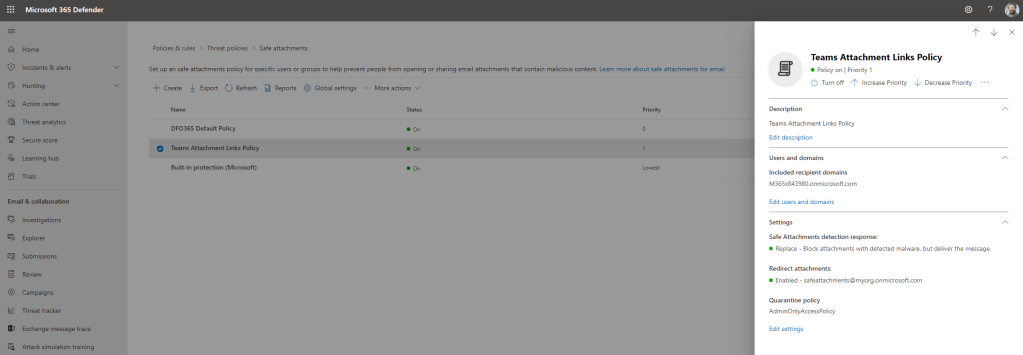
LINKS WITHIN ATTACHMENTS
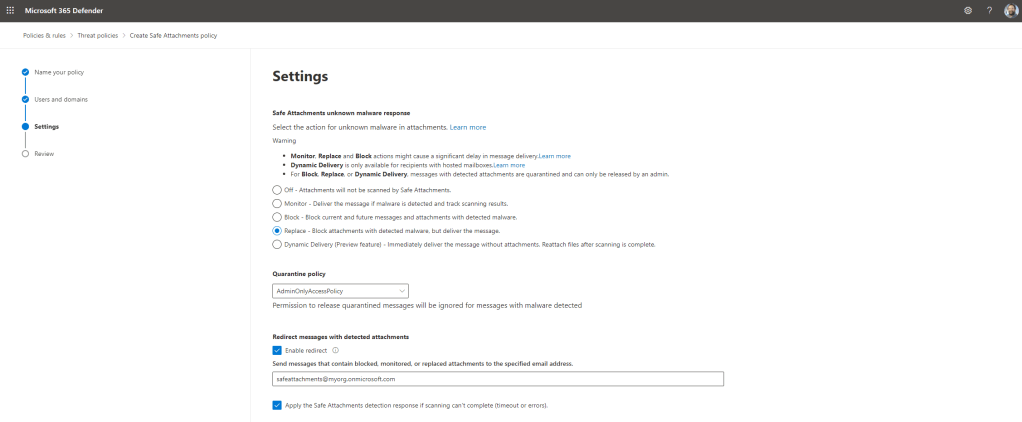
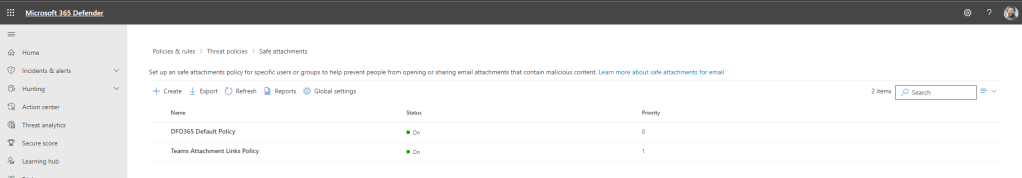
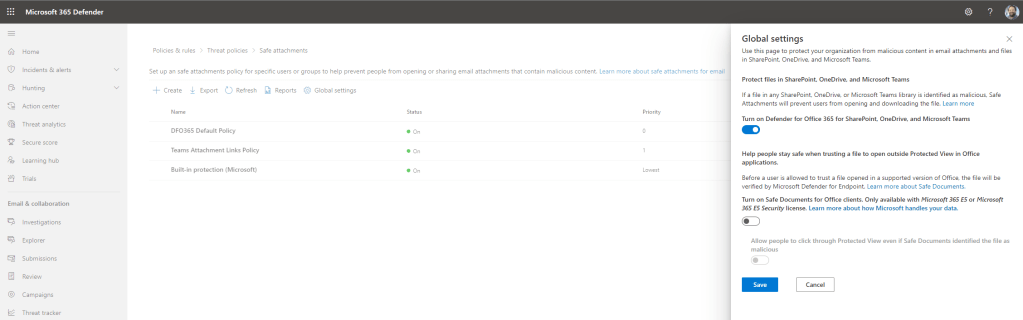
Whilst we have created a Safe Links policies, the scope for this policy only covers links within Teams chats and conversations. Links within attachments are covered within a subsequent Safe Attachments policy. This is also created within the Microsoft 365 Defender portal under Threat Policies. Remember also in the global settings for Safe Attachments to Turn on Defender for Office 365 for SharePoint, OneDrive, and Microsoft Teams which scan files in libraries (the files tab in Teams) where documents may also contain malicious file links.
HOW TO MODIFY THE SAFE LINKS POLICY PRECEDENCE
Should you have multiple Safe Links policies you can amend them by simply selecting the policy and then select Increase Priority or Decrease Priority dependent on what you want to achieve. With Safe Links and Safe Attachments the highest priority is zero (0).
REPORTING ON TEAMS SAFE LINKS
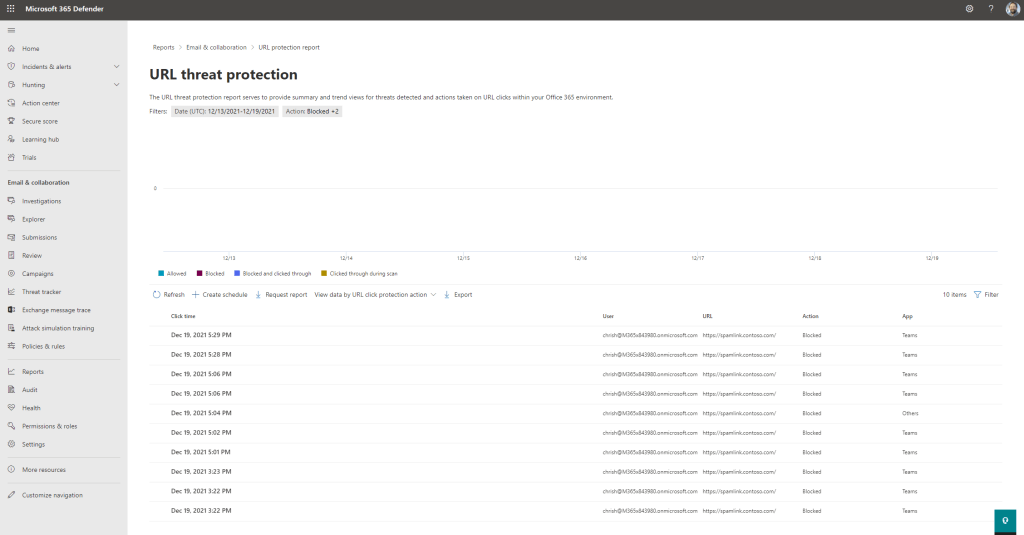
Within Safe Links with Threat Policies select Reports which will take you to the URL Threat Protection report. This will list the URL’s, the user who clicked on the URL, the resulting action and the App, in this case Teams


One thought on “Teams Real Simple with Pictures: Setting up Safe Links for Teams”
Comments are closed.