Note: This blog is now archived, and has been kept purely for historical and reference purposes. Updated blogs on this subject may appear on site in the future.
This blog is part of a series on Teams. For more articles, check back often
Written: 26/12/2021 | Updated: N/A
Happy Christmas! I hope you have enjoyed the last few days – and whether it has been with family, friends, going shopping, eating out, going to church, taking exams or feet up binge watching movies and taking a real break from everything I really hope you have managed to spend it how you have wanted to after a full on 2021. You deserve it. Me? I’m spending most with my family, but during the holidays I’m also taking some a bit of time to clear the decks for 2022 and refocus on several things which I’ve missed doing this year. One of those things is the Microsoft Tech Community. Tech was where I first started out doing community work back in late 2018. I did it compulsively right up until the beginning of 2021 and it’s been a big part of my life the past few years. It’s a place where I met a lot of my community friends: people like Adam Deltinger, Chris Webb, Juan Carlos Gonzalez Martin, Vasil Michev and Linus Cansby. Its a place where I got the opportunity to help people directly. It’s also the place which led to many more opportunities including Teams Nation. Yet with everything else going on this year – work, events, exams, speaking on the circuit, you name it – it’s been tough to allocate the time in order to really get back into it like I used to. So I needed to change things up in order to get back to the start, and having re-engaged the last few weeks I feel much happier and sharper. Now one of the questions I was asked was regarding Terms of Use. This is fortunate considering I am teaching Microsoft SCI Fundamentals next month and it’s a component of that. Terms of Use is an Azure AD functionality but applies to many services including Microsoft Teams. Do you require employees or guests to accept your terms of use policy before getting access? Do you require employees or guests to accept your terms of use policy on a recurring schedule per your compliance policies? Do you require employees or guests to accept your terms of use policy as part of a conditional access policy? Once you use it, it seems strange that you wouldn’t want this in place to ensure anyone who is accessing your environment is accepting your terms – especially as it’s an Azure AD P1 functionality and available to small businesses as well as large
Let’s go.
This blog will cover
- Setting up Terms of Use
- End user experience
- Accessing Terms of Use reports
- Notes
Note this blog may have some abridged steps which will assume some experience with a Microsoft 365 environment and Azure AD
Prerequisites
- Azure AD Premium P1, P2, EMS E3, or EMS E5 subscription
- Global Administrator, Security Administrator or Conditional Access Administrator role
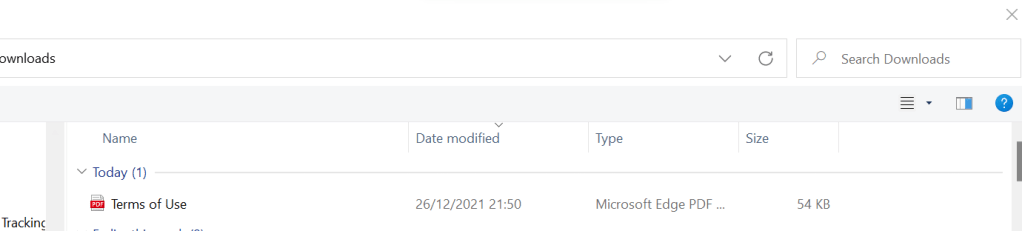
- Terms of Service PDF (Font is recommended at size 24 for mobile)
SETTING UP TERMS OF USE
1.) Login to https://login.microsoftonline.com

2.) From the waffle, or from the left app rail, select Admin
3.) In the Microsoft 365 admin centre, from the left navigation, select Show All and then Azure Active Directory
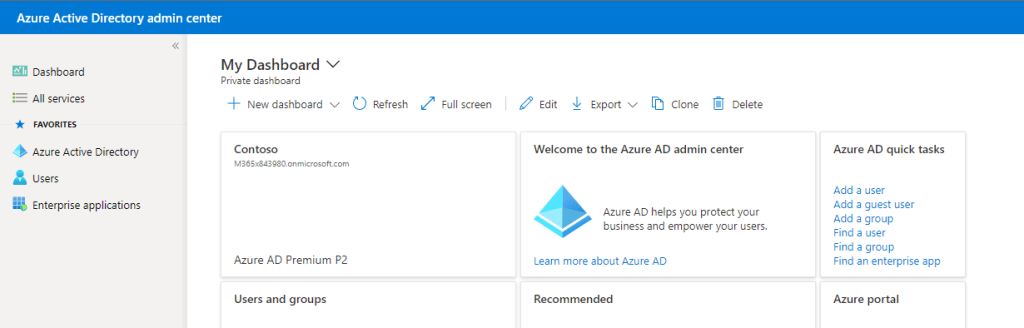
4.) From the left nav, select Azure Active Directory
5.) Select Identity Governance
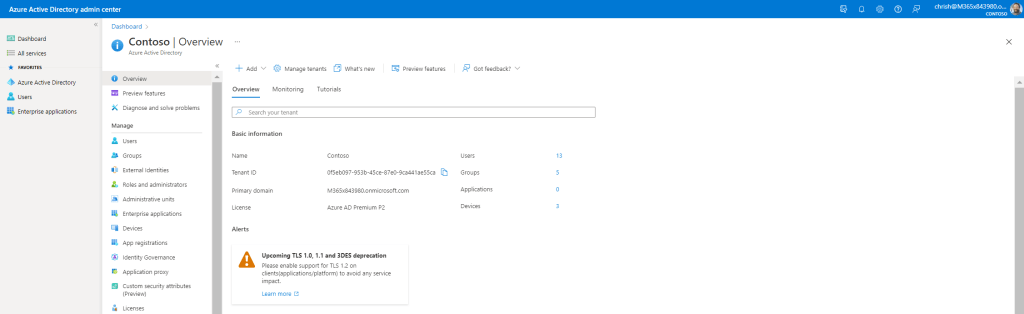
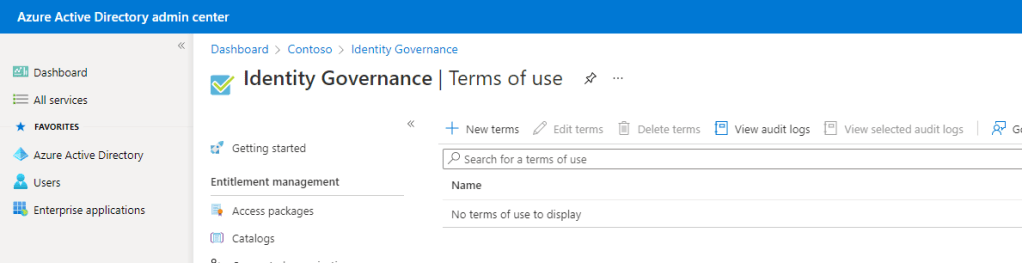
6.) Select Terms of Use
7.) Select New Terms
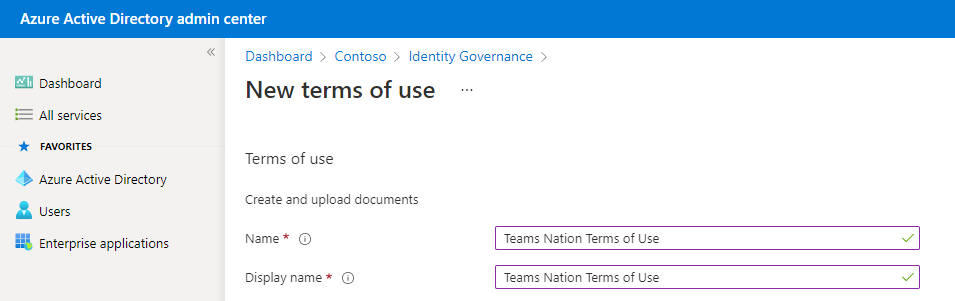
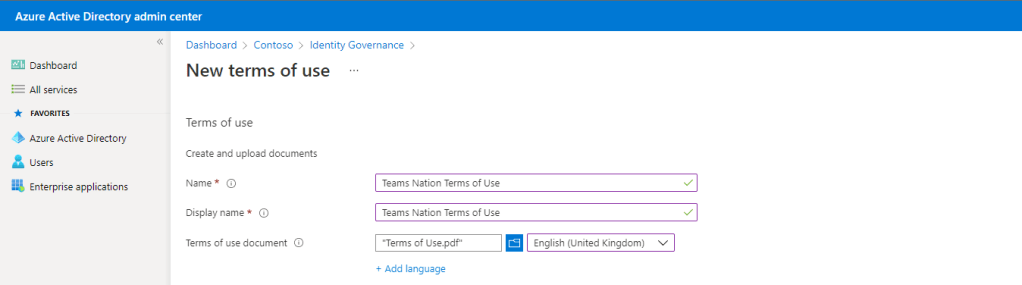
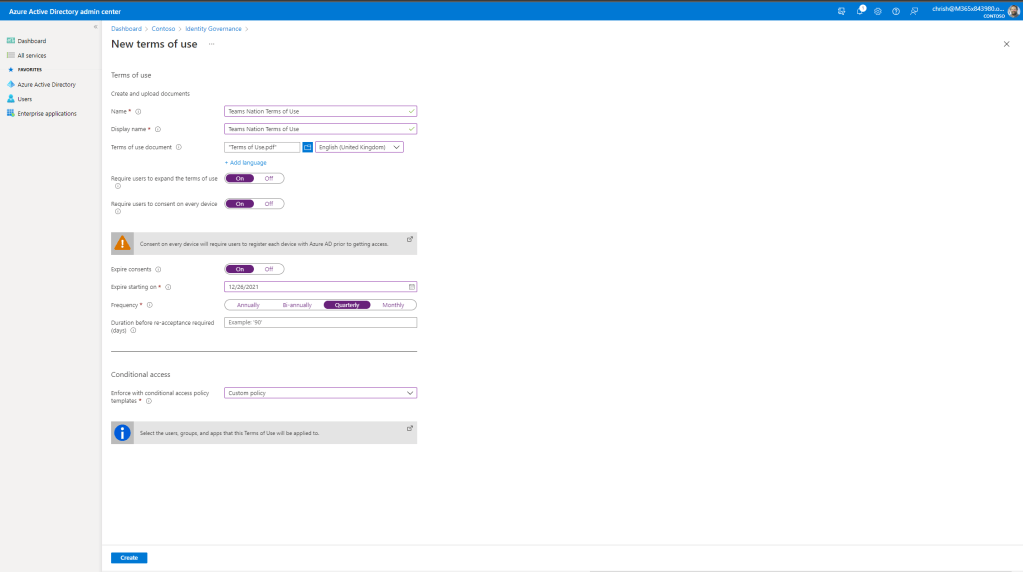
8.) Set a Name and Display Name for the Terms of Use (Here called Teams Nation Terms of Use)
9.) Upload the PDF and set the default language. Add languages if required
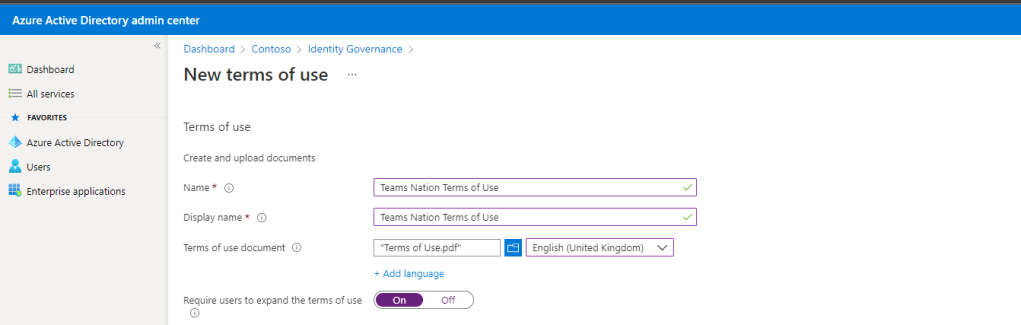
10.) Set Require Users to expand the Terms of Use to On if you want to ensure users read before accepting
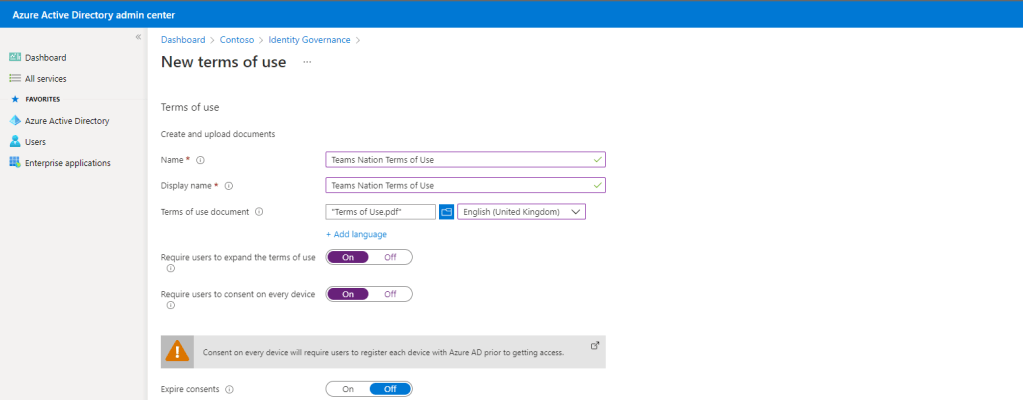
11.) Set Require Users to consent on every device to On if you want to ensure that users accept on every device they are accessing the service
Important note: A warning shows that if this is set to on users will be required to register their device in Azure AD. This needs to be set with caution as it may impact the user experience: especially if they are accessing Microsoft 365 via a browser in Incognito. From experience, in the Edge browser session you will need to be logged into EDGE with your work account. In addition, Per Device Terms of Use has some constraints, refer to the section Notes below
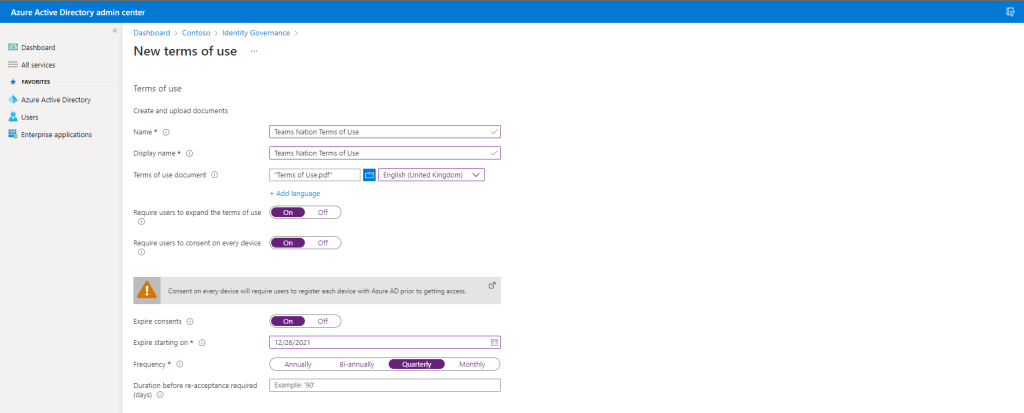
12.) Set Expire Consents to On should you need the Terms of Use to be re-consented by users on a regular basis. Here, it has been set to start today and expire on a quarterly basis which means users will need to reconsent 4 times a year. This is good to remind them of the Terms of Use
13.) Finally, under Conditional Access select Custom Policy, then select Create
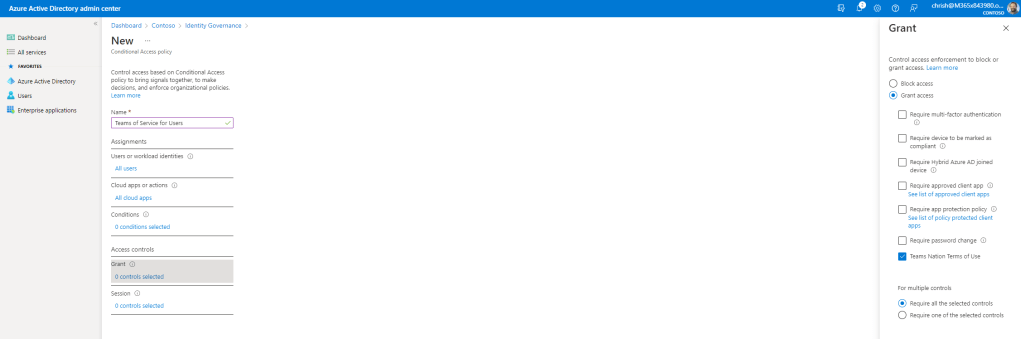
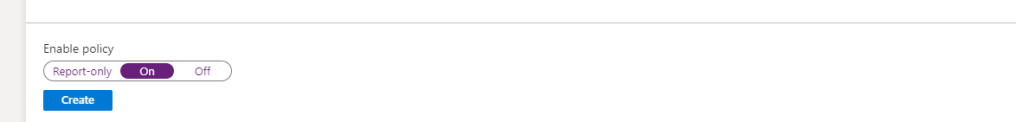
14.) Add a Conditional Access Policy as follows, Provide a Name, assign to All Cloud Users and All Cloud Apps and then under Grant select the Terms of Service you just created. Once done, Enable the policy and then select Create. Of course, at this point you could also add other things to your Conditional Access Policy such as enforcing MFA, or simply make the conditional access apply only to an app such as Microsoft Teams
Important Note: You do not want to lock yourself out. If you are applying a conditional access policy to all users its really important here to apply an exception to a service account with global administrator permissions just in case something goes wrong so you can easily modify/remove the policy if needed
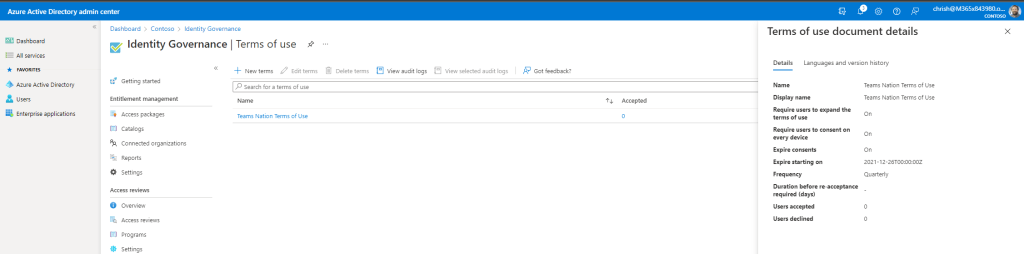
15. ) Our job here is done. The Terms of Use is now set up. Conditional Access is setup for org users, so you can go back and repeat the steps to do a second one for guests. For guests, make sure when creating the conditional access policy it is set under Users, then select Users and Groups and check All Guests and External Users
END USER EXPERIENCE
Now that the Terms of Use has been set up with a conditional access policy, users will see the Terms of Use upon accessing the service
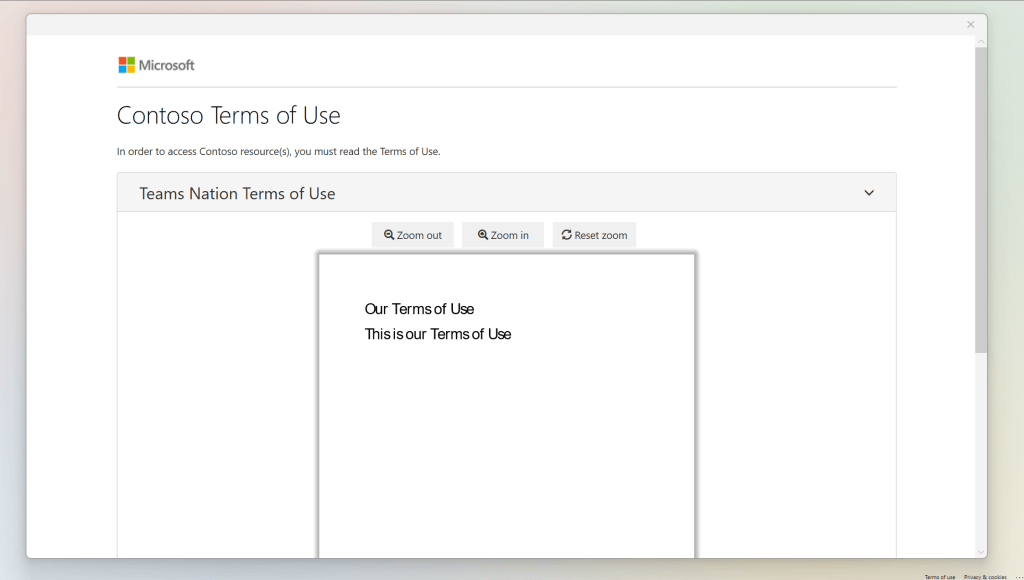
Here it is when logging into the Microsoft Teams Desktop App. Scroll to the bottom and Accept
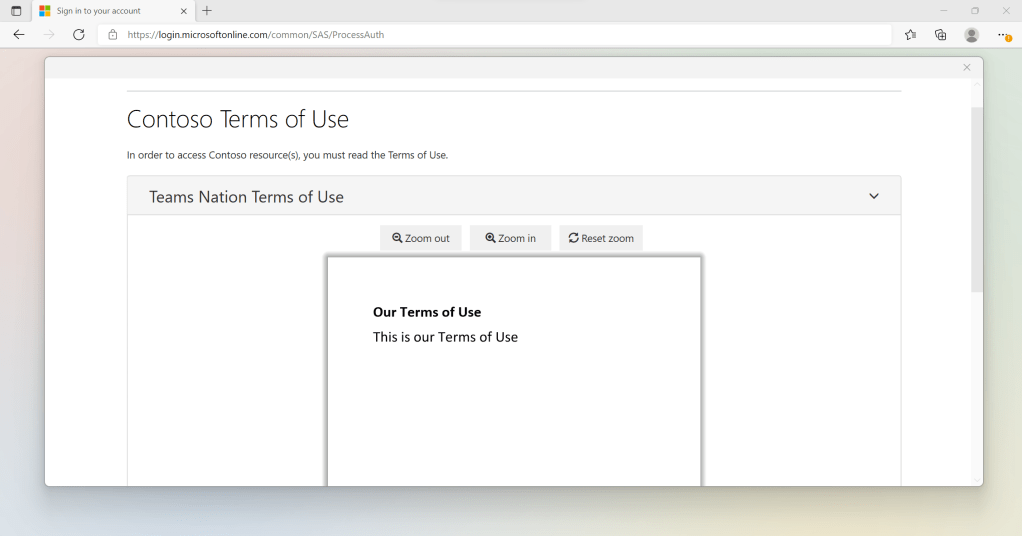
Here it is when logging into https://login.microsoftonline.com via Edge. Scroll to the bottom and Accept
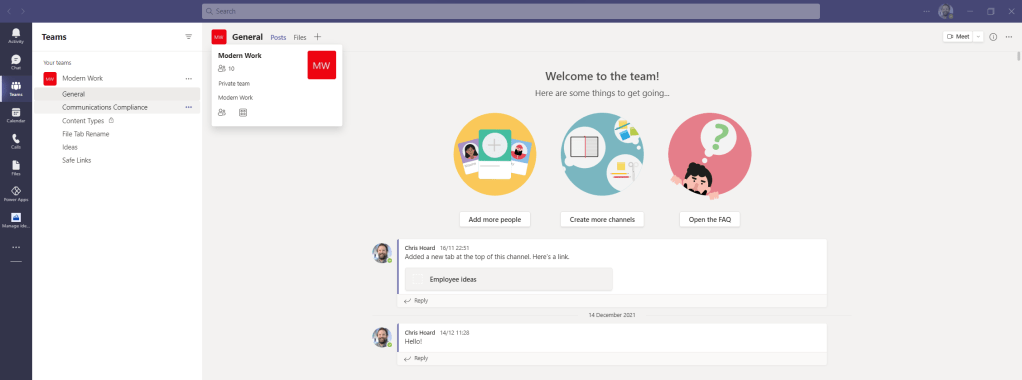
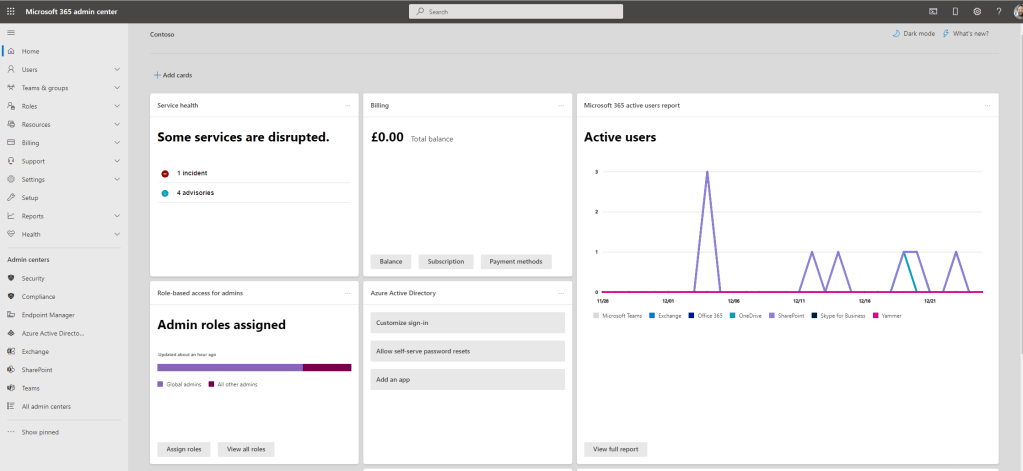
Access is now resumed to Teams (Desktop App) and the Microsoft 365 admin portal (Browser)
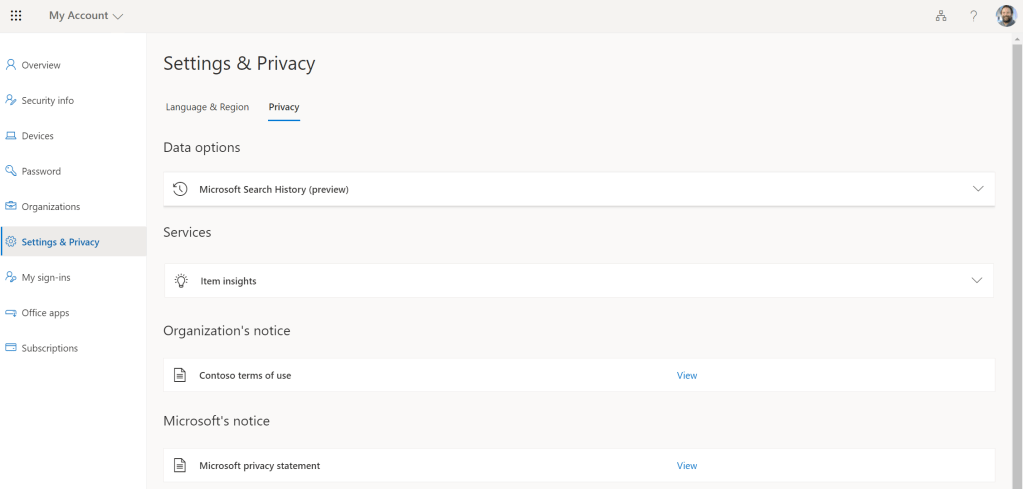
The user can always reference the Terms of Use they have signed by going to My Account. A direct link is here: https://myaccount.microsoft.com/settingsandprivacy/privacy
ACCESSING TERMS OF USE REPORTS
Now logging in successfully after accepting the Terms of Use, we need to ensure that the acceptance is logged and auditable
1.) Return to Azure Active Directory and select Identity Governance
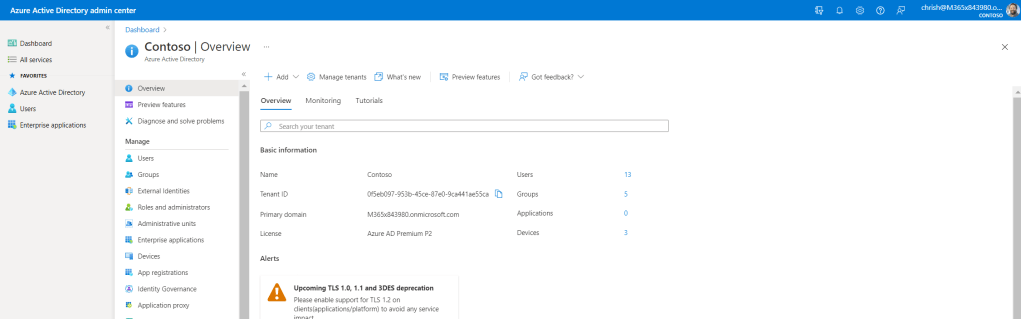
2.) Select Terms of Use

3.) The raw number of acceptances is on the right against the Terms of Use. Click on the number of acceptances to see consents
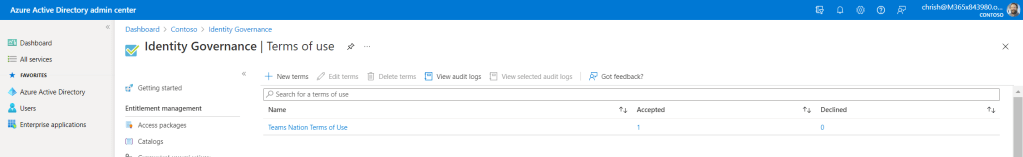
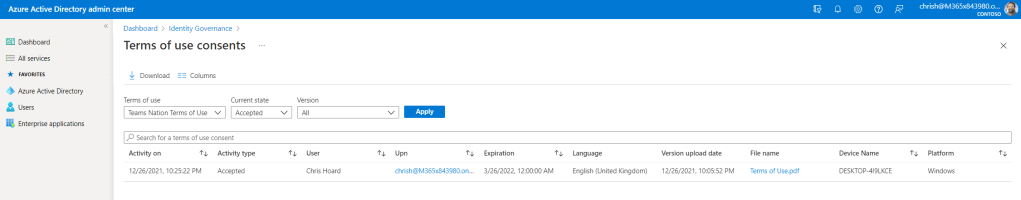
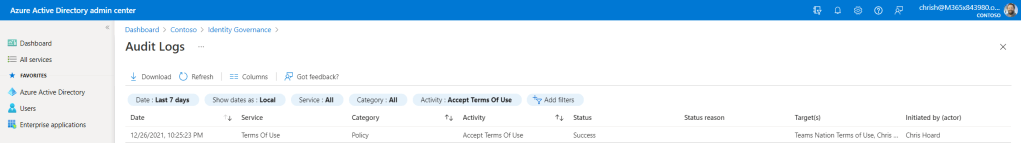
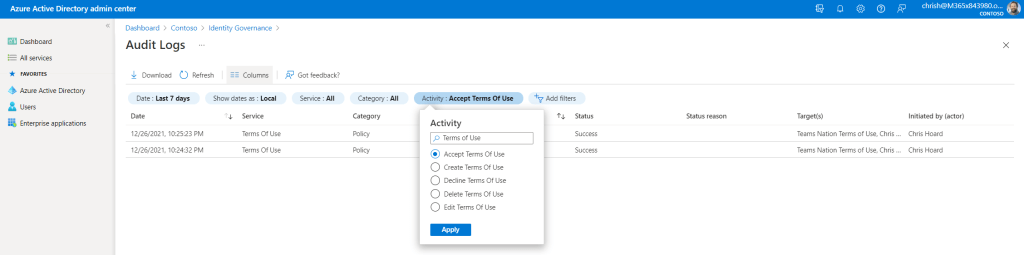
Alternatively, select View Audit Logs, filter by Activity > Accept Terms of Use. Here, you can also filter declines, creation of other Terms of Use or Deletions of Terms of Use but bear in mind the audit log is only available for 30 days
NOTES
The Require users to consent on every device setting enables you to require end users to accept your terms of use policy on every device they are accessing from. The end user will be required to register their device in Azure AD. When the device is registered, the device ID is used to enforce the terms of use policy on each device
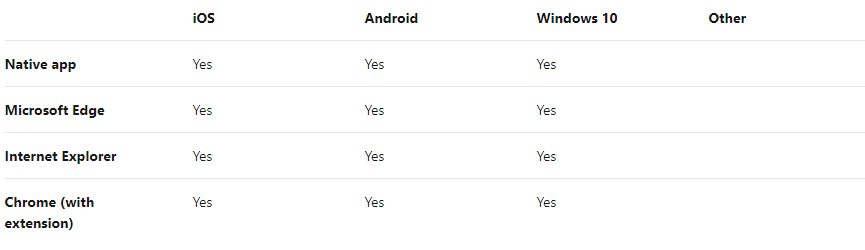
Per-device terms of use has the following constraints:
- A device can only be joined to one tenant.
- A user must have permissions to join their device.
- The Intune Enrollment app is not supported. Ensure that it is excluded from any Conditional Access policy requiring Terms of Use policy.
- Azure AD B2B users are not supported.
If the user’s device is not joined, they will receive a message that they need to join their device. Their experience will be dependent on the platform and software
Q: What happens if a user declines the terms of use policy?
A: The user would have to sign in again and accept the terms in order to get access
Q: I cannot sign in using PowerShell when terms of use is enabled.
A: Terms of use can only be accepted when authenticating interactively. Therefore this needs to be done before any PowerShell sessions
Q: Why do I see a different number of consents in the terms of use report vs. the Azure AD audit logs?
A: The terms of use report (clicking on the number of accepted on declined) is stored for the lifetime of that terms of use policy, while the Azure AD audit logs are stored for 30 days
Q: Can a terms of use policy support multiple languages?
A: Yes. 108 different languages can be configure for a single terms of use policy
Q: What happens if I’m also using Intune terms and conditions?
A: The user will be required to accept both

