This blog is part of a series on Teams. For more articles, check back often
Written: 04/04/2021 | Updated: N/A
A real short one this week – for two reasons. The first is that I am on annual leave – and whilst annual leave may conjure up the romantic idea of taking a break, this is when I usually crack on with the long list of things which I need take care of at home. This Easter weekend has included completing a 6 x 8 concreate base for a shed, and putting up a large trampoline in the back yard for my son. Secondly, I was all up for writing an in depth blog for Viva Connections – and I started doing that until I realised that the SharePoint app bar hasn’t surfaced in my demo tenant yet. I decided I didn’t want to push something out that I wouldn’t be ultimately happy with. So in the meantime I was searching for something to write about when I saw that the ability to control meeting backgrounds has now come to the TAC. For some time this has only been available in PowerShell – and whilst this blog will literally be up there with the shortest I have ever written, the functionality is really important to consider for all organisations. Why? You see when custom backgrounds were first released there were a lot of people on social racing to advocate how these could be back doored on windows machines. And whilst I agree they were great for identity and personalisation, and great for marketing and buy-in in regards to adoption, I also agree they can be problematic for IT admins. How can they be policed? How could you stop someone in your organisation uploading something offensive as a background? Whilst I hope you haven’t seen anything offensive I personally have. I’ve seen someone outside my organisation using a hospital ward as a background because they thought it was funny to do so during lockdown. I’ve seen another – again outside my organisation – using politicised images which aren’t appropriate nor professional for any type of meeting. Where have they got those images from? Are they commons or are they copyrighted? So we need to make a call, especially as Microsoft Teams does not screen backgrounds which are uploaded by users. Surfacing these in the TAC is good in that it brings attention to these controls, but also helps admins which, let’s face it, don’t like PowerShell or don’t read Docs all too often. Every IT admin now has the ability to easily control backgrounds based on the tools they like to use
This blog will cover
- Setting custom backgrounds in the global org wide meeting policy
- Setting custom backgrounds in a custom policy
Note: custom backgrounds are not available currently for all Teams clients. See here
Prerequisites
- Teams Administrator, Teams Communication Administrator or Global Administrator Permissions
- Teams Licence (usually within Office/Microsoft 365 licence) to test
SETTING CUSTOM BACKGROUNDS IN THE GLOBAL ORG WIDE DEFAULT MEETING POLICY
This will show you how to amend your custom background settings in the global org wide default meeting policy, however the same process can be used for any custom policy in place. Note that the global org wide default policy is the one applied to all users when they are first setup in Teams and which is overruled in policy precedence by custom policies directly assigned to users, policy packages and group policies. If you are unsure, check your users in the Teams Admin Centre and which policies they have applied
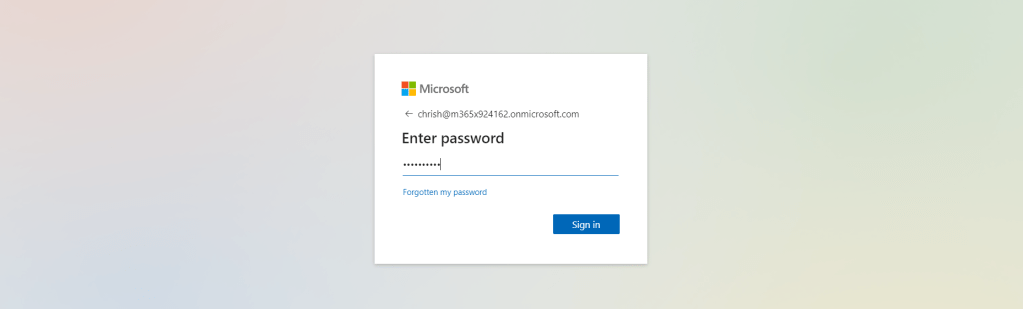
1.) Login to https://login.microsoftonline.com with admin credentials
2.) On the left app rail, select Admin
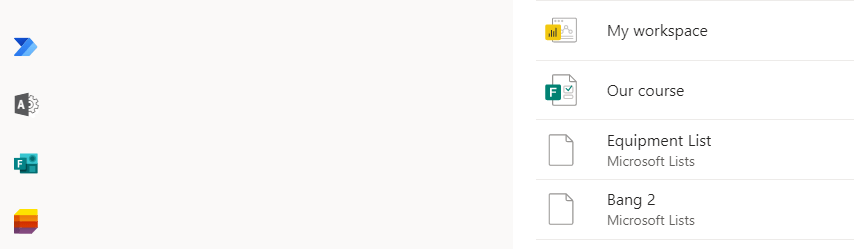
3.) On the left navigation select Show All and then select Teams
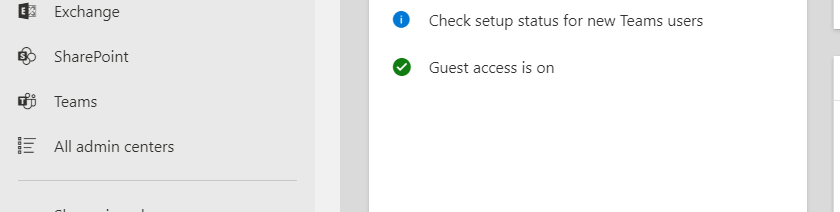
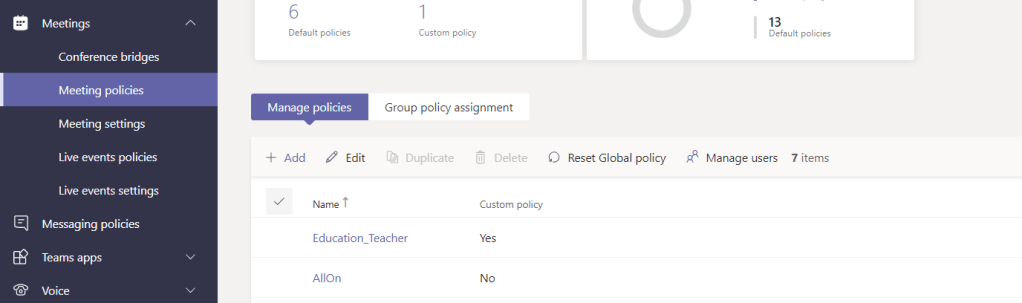
4.) In the Teams Admin Centre select Meetings and then Meeting Policies
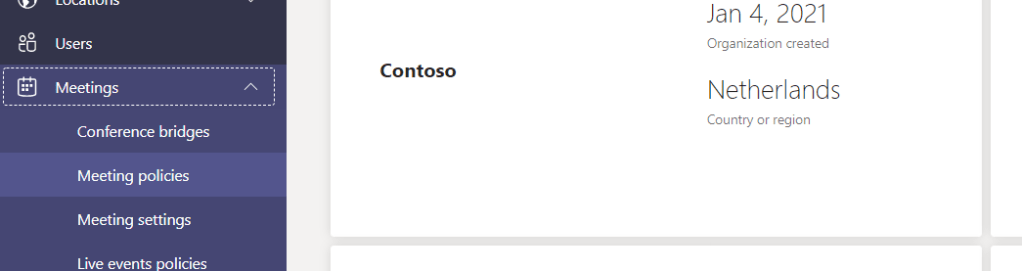
5.) Select Global (Org-Wide default)
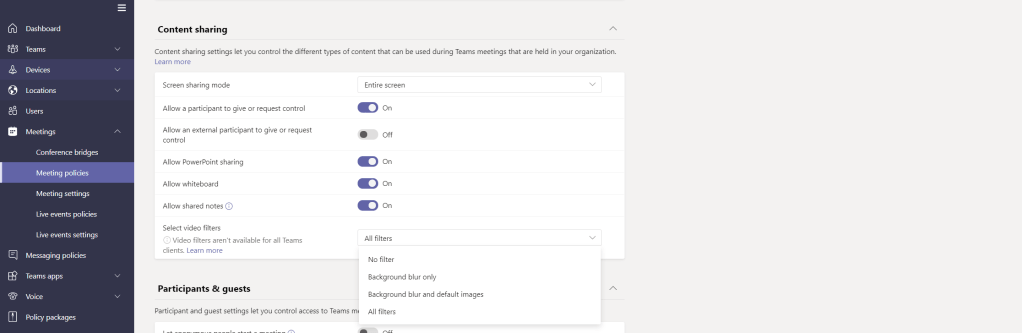
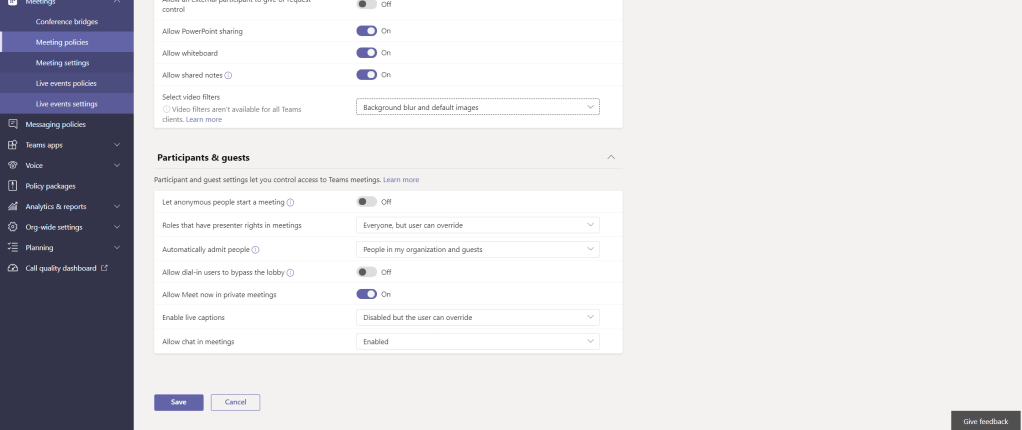
6.) Scroll to the bottom and under Content Sharing you will see Select Video Filters.
From the dropdown, you can select
- No Filter: the user cannot use any backgrounds, including background blur
- Background Blur Only: the user can use Background Blur, but no custom backgrounds
- Background Blur and Default Images: the user can use Background Blur and custom backgrounds prepopulated by Microsoft but cannot upload images
- All Filters: the user can use Background Blur, custom backgrounds prepopulated by Microsoft and can upload their own images
Once done, select Save
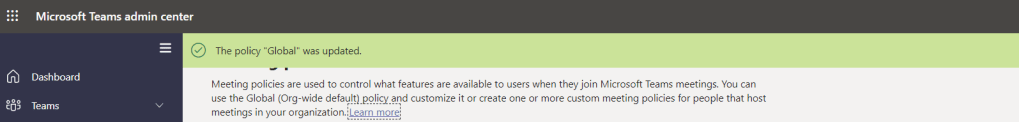
7.) Successful application of the policy should be confirmed and the policy applied to the users within a few hours
SETTING CUSTOM BACKGROUNDS IN A CUSTOM POLICY
Custom policies are useful if you want to apply different settings to different users. For example, you may permit some users to apply custom backgrounds whereas most others cannot.
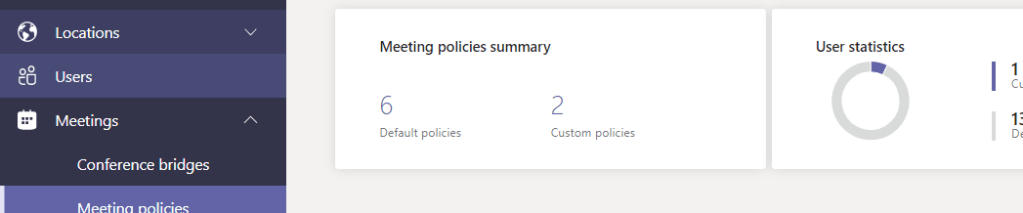
1.) In order to create a custom policy, in the Teams Admin Centre select Meetings and then Meeting Policies
2.) Select Add
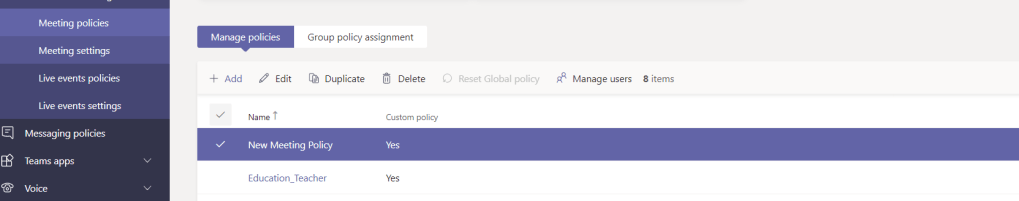
3.) Set the policy settings including the setting for Video Filters (custom backgrounds) and once done, select Save
4.) The new policy is now created
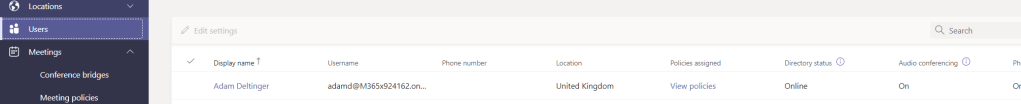
5.) Whilst you can add this to users in a number of ways including direct (individual or batch), policy package or group policy, this will simply show you how to directly apply it to an individual. From the left navigation, select Users
6.) On the user select View Policies
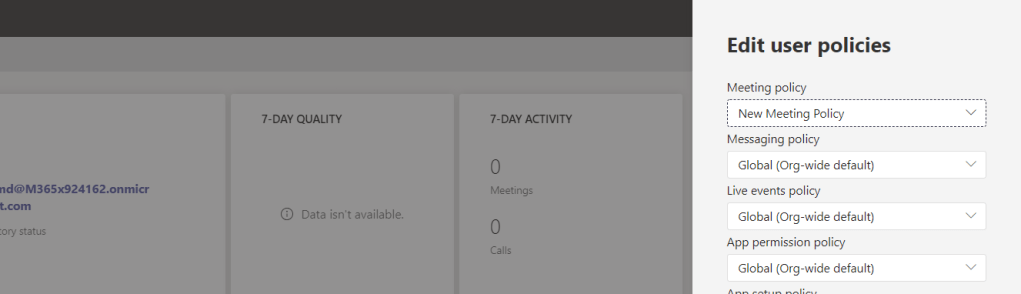
7.) Next to Assigned Policies, select Edit
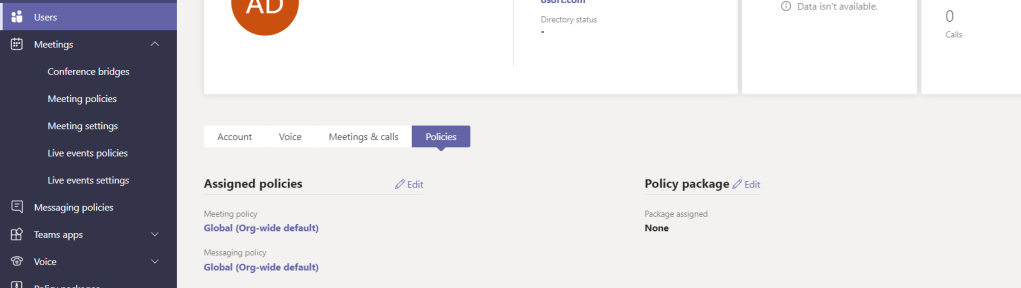
8.) Amend the Meeting Policy and select Apply
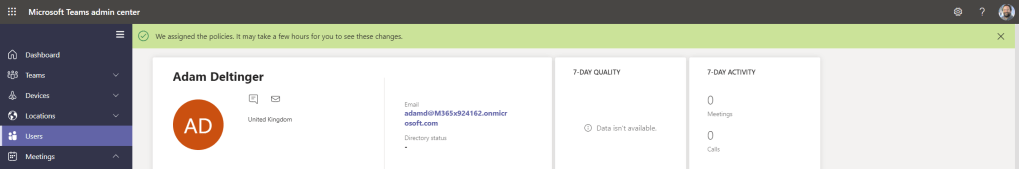
9.) The policy will then be applied to the user. Whilst the policy will usually take a few hours, it can take up to 24
Concluding remarks
This is a nice under the radar add to the Teams Admin Centre. Of course, this can still all be done in PowerShell using the Set-CsTeamsMeetingPolicy and -VideoFiltersMode commands, however, this allows all Teams admins of all skill levels to now be able to manage their organisations backgrounds in Teams quickly and easily. There is, as always, still places where this functionality can be taken. One example is letting IT determine the default set of backgrounds available for the organisation in a similar manner to how Teams templates are managed. Another is the ability to organise backgrounds into sets/categories. Another is consistency in functionality across Teams clients. However, this is a small albeit important step forward from a management perspective


6 thoughts on “Teams Real Simple with Pictures: Using the TAC to manage users backgrounds in Teams Meetings”
Comments are closed.